Top 7 DevSecOps Tools Every Security-Minded Engineer Should Master
Get a free topical map and start building content authority today.
DevSecOps tools help teams integrate security into every stage of software delivery. This guide explains the seven essential categories of DevSecOps tools, why each matters, and how to choose tools that scale with engineering needs and risk profiles.
- Detected intent: Informational
- Primary keyword: DevSecOps tools
- Secondary keywords: security automation tools; shift-left security tools
- How do SAST and DAST differ in a CI/CD pipeline?
- When should a team introduce software composition analysis?
- What are practical steps to secure Infrastructure as Code?
- How to balance runtime protection with developer velocity?
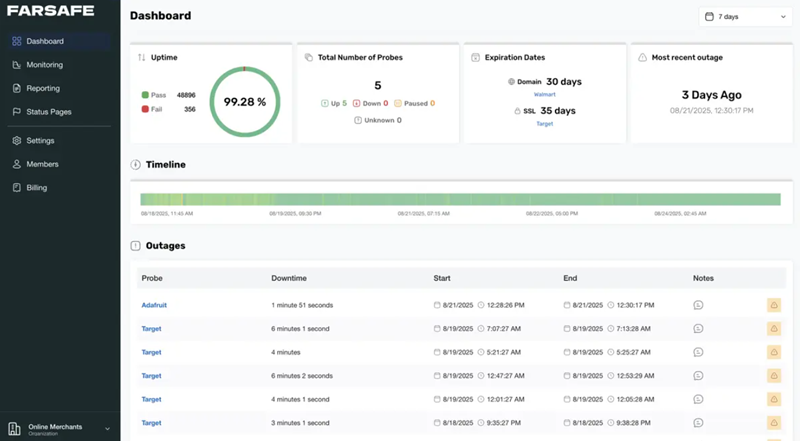
- Which metrics show that DevSecOps tools are effective?
DevSecOps tools: the 7 categories every team should know
Understanding DevSecOps tools by category makes selection and integration predictable. The seven categories below cover discovery, prevention, and detection across the software lifecycle.
1. Static Application Security Testing (SAST)
SAST analyzes source code or compiled artifacts to find vulnerabilities early. These shift-left security tools run during local builds and CI to catch injection flaws, insecure deserialization, and unsafe cryptographic usage before release. Typical trade-offs: fast feedback vs. noise from false positives.
2. Software Composition Analysis (SCA)
SCA inspects third-party libraries and open-source components for known vulnerabilities and license issues. Integrating SCA into PR checks prevents vulnerable packages from entering the codebase. Related entities: CVE databases, artifact registries, SBOM (Software Bill of Materials).
3. Dynamic Application Security Testing (DAST)
DAST evaluates running applications from the outside-in, simulating attacks against endpoints. Use DAST in staging and pre-production to validate runtime behavior and API security. DAST complements SAST by finding issues that only appear in a running environment.
4. Infrastructure as Code (IaC) scanning
IaC scanning inspects Terraform, CloudFormation, Kubernetes manifests, and similar templates for misconfigurations (open S3 buckets, excessive IAM privileges). These security automation tools reduce cloud drift and ensure secure defaults before deployment.
5. Secrets management and identity tools
Secrets managers and identity controls (vaults, hardware-backed keys, robust RBAC) prevent credential leakage and remove hard-coded secrets from repos. Combine with CI/CD credential injection and short-lived tokens to reduce blast radius.
6. Container and registry scanning / CSPM
Container scanning checks images for vulnerable packages; registry policies prevent pushing images that fail checks. Cloud Security Posture Management (CSPM) tools monitor cloud resource configuration at scale. These tools bridge build-time scanning and runtime posture management.
7. Runtime detection and response / observability
EDR/KSPM/runtime application self-protection (RASP) and centralized observability detect anomalous behavior, intrusion attempts, and misconfigurations in production. Instrumenting telemetry and alerting enables fast incident response and post-incident analysis.
Framework and checklist: apply NIST SSDF and a 7-point selection checklist
Use established frameworks for decision-making. The NIST Secure Software Development Framework (SSDF) defines practices for integrating security across the development lifecycle and is authoritative for secure-by-design claims. For implementation guidance and best practices, see the NIST SSDF overview: NIST SSDF.
Implementation checklist — "7-point DevSecOps Tool Selection Checklist":
- Does it integrate with existing CI/CD (PRs, pipelines, registries)?
- Does it provide actionable results with acceptable noise levels?
- Can it scale with repos, teams, and cloud accounts?
- Does it support automation (APIs, IaC scanning, policy-as-code)?
- Does it map results to known standards (CWE, CVE, MITRE ATT&CK)?
- Is role-based access control and audit logging available?
- Are licensing and operational costs predictable?
Practical tips for integrating DevSecOps tools
- Start with low-friction integrations: enable SCA and SAST in PR gates, then expand to IaC and DAST.
- Configure tools to fail builds only on high-severity issues initially; tune rules over time to reduce developer friction.
- Automate triage: map tool findings to an issue tracker and assign ownership using tags for severity and component.
- Keep a baseline SBOM and scan artifacts in the CI pipeline rather than relying solely on runtime discovery.
- Measure impact: track mean time to remediate (MTTR) and number of vulnerabilities introduced per release.
Trade-offs and common mistakes when choosing tools
Choosing tools involves balancing security coverage, developer productivity, and operational cost. Common mistakes include:
- Deploying too many tools at once, creating alert fatigue.
- Ignoring integration: tools that don't fit CI/CD or ticketing systems become manual chokepoints.
- Over-reliance on a single category (e.g., only SAST) while missing runtime threats.
- Failing to tune rules, producing excessive false positives and eroding trust.
Real-world scenario
A small fintech team adopted a phased approach: first, enable SCA scans and secrets scanning on all PRs; second, introduce SAST checks that run on nightly builds; third, block images with critical vulnerabilities from the registry. Using the 7-point checklist ensured CI integration and predictable costs. Within three sprints the team reduced high-risk open-source dependencies by 60% and cut the average time to remediate critical findings from 10 days to 48 hours.
Related terms and technologies to know
Familiarity with SAST, DAST, SCA, IaC, CSPM, KSPM, SBOM, CI/CD, RBAC, OAuth, JWT, CWE, CVE, MITRE ATT&CK, and observability platforms helps in evaluating and integrating DevSecOps tools effectively.
FAQ
Which DevSecOps tools should a small team start with?
Start with SCA for third-party dependency checks and secrets scanning to prevent obvious supply-chain and credential risks. Add SAST in CI for core codebase checks and introduce IaC scanning before provisioning cloud resources.
How do security automation tools reduce developer burden?
Security automation tools shift detection and enforcement into CI/CD, providing automated checks, policy-as-code, and ticket creation so developers receive actionable guidance inside their workflow rather than manual triage steps.
How to measure the effectiveness of DevSecOps tools?
Track metrics such as MTTR for vulnerabilities, percentage of releases blocked by high-severity issues, number of false positives, and trends in vulnerability counts per component. Correlate tool alerts with incident postmortems to validate detection value.
What common mistakes cause rollout failure?
Rolling out too many tools at once, failing to integrate results into developer workflows, not tuning severity thresholds, and lacking clear ownership for triage are common causes of poor adoption.
How do shift-left security tools fit into a CI/CD pipeline?
Shift-left security tools (SAST, SCA, IaC scanning) run earlier in the pipeline—during local builds, pre-commit hooks, and PR checks—preventing vulnerabilities from reaching later stages and reducing remediation cost.