Developing a Secure Platform for IoT Standards
Get a free topical map and start building content authority today.
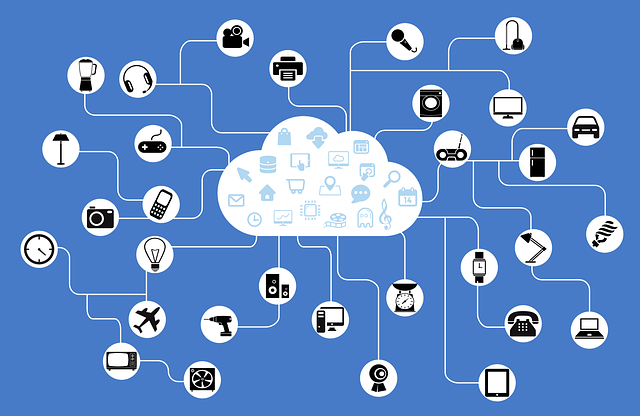
The Internet of Things (IoT) refers to a network of devices and software that connect via a dynamic host configuration protocol server to exchange and store data. Examples include smart camera, automation systems, and wearables.
IoT technology has infiltrated just about every home and business throughout the country due to its convenience and capabilities. In fact, it's estimated that there will be 500 billion connected devices by 2030. However, whenever you have an interconnected system, you want reassurance that it is secure, especially in the workplace. Learn more about developing a secure platform for IoT standards.
How IoT Improves Business Operations
IoT devices and technology are becoming commonplace in most industries for several reasons.
First, IoT can help automate many tasks throughout your day. This allows your employees to be more productive and get more done than they did before. You may even be able to save money on employees. For example, you can set up security cameras to give you alerts if it detects anyone on your premise so that you don't have to hire security guards to watch the cameras for you.
IoT communication and connectivity can also make it easier for employees to share necessary information with each other. The employees can access the information more quickly for clients, increasing customer satisfaction and saving time for the employees.
You will also be able to monitor employee activity, making it easier to hold employees accountable and ensuring quality service.
Identifying IoT Security Risks
If you are wondering how to secure IoT, you first need to understand its vulnerabilities and how to spot them. Any time you have multiple devices connected, there are multiple points of vulnerability.
Hackers may be able to infiltrate your system to gain access to sensitive data, such as customer information. They can also take over your system to make it ineffective. For example, a hacker may enter your security camera to turn it off before a robbery.
A PWC report recently found that 93% of executives believe that the benefits of an IoT system drastically outweigh the risks.
How to Ensure Secure Communication with IoT Devices
Get the reassurance that your network will be properly established by hiring an Internet of Things development company to establish your network for you.
It's important to start with devices that already have built-in security features. Many devices don't have safeguards. Keep in mind that even one insecure device can leave the entire system vulnerable. Therefore, all devices on your network should have adequate security features. It's important to consider industry security requirements when choosing devices for your network, too. Certain industries, such as healthcare, must adhere to more advanced security measures than others. You can find devices that are made to be HIPAA-compliant.
Many devices have security measures included in their software. You may need to perform regular upgrades to ensure that any new security features are downloaded to your device. You may have to do this manually. Even if most of the devices perform upgrades automatically, you should still be sure to verify that all upgrades were successful regularly (once a month or once a quarter). Having a regular maintenance schedule will ensure that you stay up to date.
During your network maintenance, an IT tech should also check for any potential threats to the system. To do this, you will need a trained IT tech to have full access to the system, where they can monitor activity and provide you with a report. This report can help you make any required changes in your daily operations to eliminate the threats. You may also want to include additional security to alert you of threats as soon as they happen.
After securing IoT devices, you also need to secure the data you're storing in the cloud with IoT cloud security. Securing IoT data should be of utmost importance to you if you store customer information or other sensitive information. A security breach can have disastrous consequences to your company if the customers find out. Customers may not want to do business with your company for fear of their information getting hacked. If their information does get hacked, you may end up getting sued on top of it.
You should also train your staff on how to use the devices and data on your IoT network securely. You should also have clear policies in place regarding what devices can be connected to the system and which cannot. Be sure that all employees accessing the system have a unique login so that everyone can be held accountable for their activity if necessary.
Using IoT Devices to Secure Communication
The IoT devices you purchase can be used to enhance the security of your internal and external communications with their built-in security features.
You can also take the following steps to increase communication security:
1. Use secure user names and passwords: Establish a login system at your office that requires all users to choose a secure username and password. Make sure employees know not to write their password down at their desks, where it can be easily accessed.
2. Enable encryption: Encryption means that data is blocked from view until a secure user accesses it. Even if someone manages to access the account, they won't be able to see the information unless they put in an authorized username and password.
3. Connect all devices to a secure network: Your IoT system is only as good as the network its connected to. Keep your internet connection secure to keep your IoT devices and data secure.
Conclusion
When you utilize IoT at your place of business, you can increase your competitive edge. However, you may also create vulnerable spots where hackers can access information. Protect IoT devices by buying devices that have adequate security and updating them regularly. Leave the legwork to an IoT development company to ensure the best results.










