Practical Guide: Debug IoT App Behavior in Production
Get a free topical map and start building content authority today.
Detectable intent: Informational
Introduction: Why production debugging matters
When an application connects to fleets of devices, expectations for stability, telemetry accuracy, and security increase. This guide focuses on how to debug IoT app behavior in production without disrupting live devices or creating privacy and safety risks. The goal is to provide practical diagnostics, monitoring patterns, and incident controls that work for constrained devices, intermittent connectivity, and distributed cloud services.
- Primary goal: observe, isolate, and fix app behavior without stopping production traffic.
- Core framework: MONIT (Metric, Observability, Notification, Investigation, Triage).
- Five core cluster questions (link targets for deeper pages):
- How to capture reliable telemetry from constrained IoT devices?
- What production logging levels are safe for device fleets?
- How to correlate device events across edge and cloud services?
- How to set up alerting for IoT-specific failure modes?
- What rollback and failover patterns reduce production risk?
- Reference best practice snapshot: see NIST IoT guidance for security and lifecycle practices (NIST IoT program).
How to debug IoT app in production
Debugging an IoT app in production is a structured activity: first observe, then isolate, then remediate. Start by improving signal quality — more useful metrics, richer traces, and contextual logs — while minimizing device impact. The following sections explain a repeatable approach and the MONIT framework to keep work consistent across teams.
MONIT framework: a named checklist for production debugging
The MONIT framework is a compact model to operationalize debugging and monitoring:
- Metric — Define key metrics (device connectivity, message latency, error rates, battery level, retry counts).
- Observability — Implement tracing and structured logs; ensure telemetry includes device context and correlation IDs.
- Notification — Set actionable alerts with thresholds and suppressed flapping rules.
- Investigation — Create playbooks for common anomalies and use session replays or event reconstruction to reproduce conditions.
- Triage — Prioritize fixes by customer impact and rollback risk; schedule safe rollouts and mitigation steps.
Key techniques and tools to use in production
Instrumenting production systems requires balancing visibility and safety. Use these techniques:
- Structured logging with sampled log levels: keep debug-level logs off by default but enable sampling or per-device tracing when investigating.
- Distributed tracing across edge and cloud: attach correlation IDs to telemetry and messages to follow a request from device to backend.
- Telemetry aggregation and pre-processing at the edge: summarize high-frequency signals to reduce bandwidth and storage costs.
- Feature flags and progressive rollouts: isolate changes and rollback quickly without full redeployments.
- Canary devices and synthetic transactions: emulate device behavior to test fixes before broad rollout.
Real-world scenario: intermittent disconnects in a smart thermostat fleet
Symptom: a subset of thermostats reports repeated reconnects every 5–10 minutes and missed temperature updates. Steps to debug in production:
- Confirm scope with metrics: check device connectivity anomaly rates and cluster-specific spikes.
- Enable a short-term trace for a sampled set of affected device IDs to collect connection lifecycle events and handshake timings.
- Correlate logs with network telemetry: identify whether disconnects align with edge gateway reboots or cloud broker throttling.
- Deploy a mitigation: increase client-side backoff and route affected devices through a stable gateway via feature flag.
- Monitor impact and plan a permanent fix: patch gateway resource leak and roll out progressively.
Practical tips for safer, faster production debugging
- Use correlation IDs end-to-end: ensure every device message carries a unique ID for trace reconstruction.
- Prefer sampled debug traces over blanket debug logging to avoid storage overload and privacy exposure.
- Store enriched telemetry in a time-series database and link event indexes to logs/traces for fast querying.
- Automate alert suppression windows and runbooks for known transient events to reduce alert fatigue.
- Limit on-device debugging features via short-lived credentials and revoke access quickly after investigation.
Common mistakes and trade-offs
Trade-offs to consider
- Visibility vs. cost: high-cardinality telemetry is useful for root cause analysis but increases storage and query costs.
- Telemetry frequency vs. device resources: verbose telemetry helps diagnosis but drains battery and bandwidth on constrained devices.
- Immediate remediation vs. safe rollback: urgent fixes can introduce regressions; prefer targeted mitigations and staged rollouts.
Common mistakes
- Relying on raw logs without correlation IDs, making cross-service tracing impossible.
- Not having an automated canary or synthetic device, which delays detection of regressions.
- Over-alerting on noisy signals without grouping; teams miss important incidents due to alert fatigue.
- Changing device-side logging in production without an opt-in mechanism or sampling plan.
Monitoring and alerting checklist
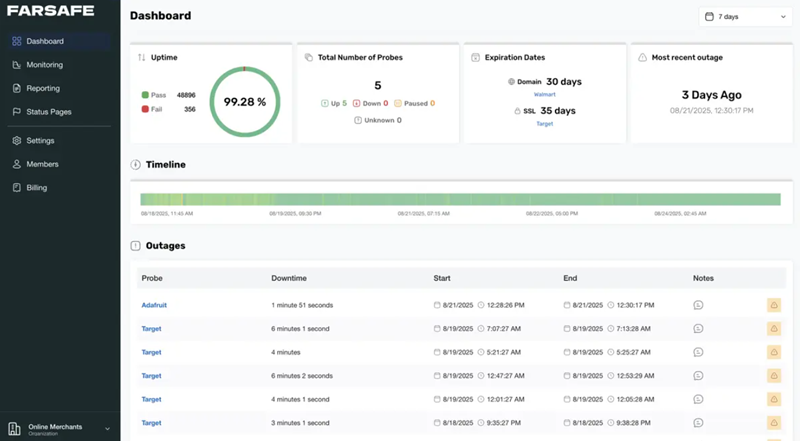
- Define SLOs for device uptime, message latency, and error budgets.
- Create dashboards for per-cluster and per-device-type metrics with percentiles and anomaly detection.
- Configure alerts with context-rich payloads including suspect device IDs, relevant traces, and suggested runbook steps.
- Run regular chaos tests on non-production and a small production canary group to validate monitoring and recovery.
Integration considerations and standards
Ensure telemetry design follows privacy and security policies. Use proven protocols (MQTT, CoAP, HTTPS) and adhere to platform identity and certificate management best practices. For guidance on lifecycle and security standards, see NIST's IoT program referenced above.
Wrap-up and next steps
Debugging IoT app behavior in production is a continuous process: improve signal collection, keep investigation lightweight and reversible, and document playbooks so incidents are reproducible. Adopt the MONIT checklist, instrument correlation IDs, and automate canary rollouts to reduce mean time to detection and repair.
FAQ: How to debug IoT app in production?
Start with high-level metrics to confirm scope, enable sampled traces for affected devices, and use feature flags or canaries for low-risk mitigations. Retain logs long enough for analysis but use sampling to limit exposure.
FAQ: How frequently should devices report telemetry to monitor IoT device behavior?
Telemetry frequency depends on use case and device constraints. For battery-powered devices, use event-driven reporting or adaptive sampling. For critical safety signals, use higher frequency combined with edge aggregation to avoid overload.
FAQ: What are safe logging levels for production IoT systems?
Keep production logging at info or warning by default. Use trace or debug levels only for sampled investigations with a clear retention and privacy policy. Consider redaction of sensitive fields before storage.
FAQ: How to correlate device logs with cloud traces?
Attach a consistent correlation ID to every device message and propagate it through edge gateways and cloud services. Store IDs in logs, traces, and message metadata for fast cross-system queries.
FAQ: Can feature flags and progressive rollouts reduce the need to debug in production?
Yes — feature flags and staged rollouts reduce blast radius and help validate fixes on canary groups before full deployment, lowering the operational burden of production debugging.