Top Alternatives to Opsgenie for Incident Management & Alerting — 2025 Guide
Get a free topical map and start building content authority today.
Top Opsgenie alternatives for incident management
Choosing the right Opsgenie alternatives is a common decision for teams that need reliable incident management, flexible on-call schedules, and effective alerting workflows. This guide compares categories of replacements, explains trade-offs, and provides a practical checklist to evaluate candidates.
Detected intent: Comparative
- Primary keyword: Opsgenie alternatives — focus on alerting, on-call, and incident workflows.
- Evaluation checklist included (based on the NIST incident response lifecycle).
- Practical tips, trade-offs, and a short selection scenario for real-world context.
Why look for Opsgenie alternatives?
Opsgenie alternatives are explored for reasons including cost control, deeper integrations with existing monitoring stacks, simpler on-call UX, or stronger automation for incident escalation. The decision should align with incident response objectives: faster detection, clearer escalation, and consistent post-incident review.
How to group and compare alternatives
Incident management tools fall into broad categories. Grouping them helps prioritize trade-offs:
- Enterprise incident platforms: Focus on scale, audit trails, and comprehensive runbooks.
- Developer-first alerting tools: Lightweight, tight integrations with code and CI/CD.
- Shared communication and collaboration apps with on-call features: Best for teams that value unified chat and incident chatops.
- Open-source solutions: Offer full control and customization at the cost of maintenance.
Evaluation checklist: NIST-based Incident Response Lifecycle
Use this named framework — the Incident Response Lifecycle (based on NIST guidance) — as a checklist when comparing Opsgenie alternatives. The checklist aligns product capabilities to incident phases.
- Prepare: On-call scheduling, runbook templates, roles & permissions.
- Detect: Integration breadth with monitoring, noise filtering, thresholding.
- Triage: Alert enrichment, contextual links (logs, metrics, traces), automated grouping.
- Respond: Escalation policies, multi-channel notifications, incident timelines.
- Recover: Collaboration tools, rollback hooks, status pages.
- Review: Post-incident reports, tracking of action items, SLA reporting.
For the authoritative incident response lifecycle reference, see NIST SP 800-61.
Feature trade-offs to consider
Selecting an alternative involves trade-offs. Consider these common choices:
- Customization vs. ease-of-use: Highly customizable systems allow sophisticated automations but require more setup and maintenance.
- Integration depth vs. vendor lock-in: Deeper proprietary integrations can speed deployment but may create dependencies.
- Cost predictability vs. feature completeness: Per-user or per-alert pricing simplifies estimates but can grow expensive as usage scales.
Common mistakes
- Choosing solely on feature lists without testing real workflows and noise levels.
- Neglecting on-call UX and notification fatigue when evaluating alert routing.
- Assuming all integrations are equal — verify depth (contextual links, bi-directional actions).
Named alternatives categories and representative options
Examples of options within each category illustrate typical trade-offs. Tool names are shown as examples of features and categories, not as endorsements.
- Enterprise platforms: strong audit logs, role-based access control, and advanced reporting.
- Developer-first tools: tight CI/CD integrations, incident-as-code workflows, on-call rotation via APIs.
- Chat-forward solutions: integrated incident channels and runbook execution from chat.
- Open-source choices: full control but require host-and-maintain approach.
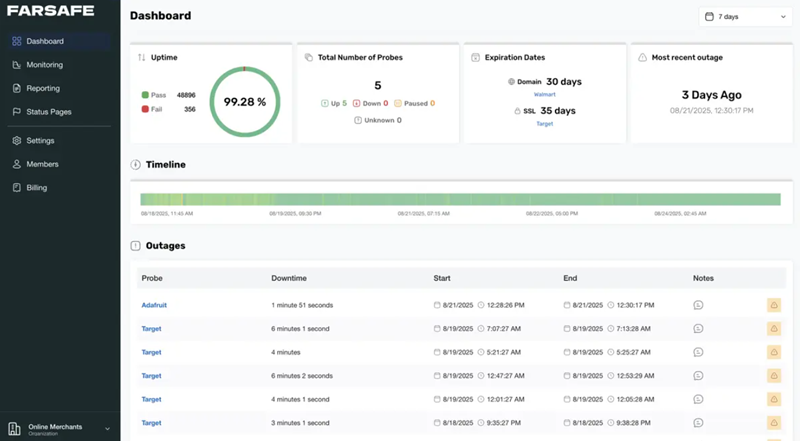
Real-world example
A mid-size ecommerce team experienced frequent alert storms from synthetic monitoring during peak hours. Using the evaluation checklist, the team prioritized noise reduction (auto-grouping) and rapid escalation. The selected alternative provided an alert deduplication layer, flexible scheduling for cross-timezone on-call rotations, and a built-in incident timeline that reduced mean time to acknowledge by 30% during simulated drills.
Practical tips for selecting an Opsgenie alternative
- Run a two-week pilot with real alerts and on-call engineers to measure noise, latency, and usability.
- Test integrations end-to-end: create an alert from a monitor and confirm linked logs, traces, and the ability to attach runbook steps.
- Measure alert volume and cost impact under expected growth scenarios; simulate peak traffic during evaluation.
- Standardize incident severity and escalation rules before migration; inconsistent rules magnify migration friction.
- Keep the rollback plan ready — switch back to previous routing for a short period while re-tuning policies.
Trade-offs and how to decide
Focus decision criteria on operational outcomes rather than feature counts. If the priority is reducing wake-ups, emphasize noise-filtering and escalation policies. If compliance and audit are the priority, emphasize immutable incident logs and RBAC. Budget-constrained teams may prefer open-source or developer-first services and accept more maintenance overhead.
Core cluster questions
- How to evaluate incident management and alerting tools for reliability and noise reduction?
- What on-call scheduling features matter most for global teams?
- How to measure total cost of ownership for an incident management platform?
- Which integrations are essential for fast incident triage and root cause analysis?
- What are the best practices for migrating on-call policies and historical incident data?
Implementation checklist before switching
- Map existing alert sources and volume by category.
- Document current escalation paths, severity definitions, and runbooks.
- Run a controlled pilot with shadow routing to compare acknowledgements and false positives.
- Train on-call engineers on the new notification channels and escalation UI.
- Plan a phased cutover with a rollback period.
Final recommendation summary
Opsgenie alternatives should be measured against the Incident Response Lifecycle checklist: prepare, detect, triage, respond, recover, and review. Prioritize a trial that mirrors production alert noise, confirm deep integrations with logging and tracing, and test the on-call UX under realistic conditions.
What are the best Opsgenie alternatives for different team sizes?
Answer depends on priorities: small teams often value low-friction setup and predictable costs; mid-size teams prioritize integrations and automation; large enterprises prioritize governance, SLAs, and auditability. Use the NIST-based checklist to weigh features against team constraints.
How to migrate alerting rules from Opsgenie without losing history?
Export current routing and escalation configurations, run a shadowing phase where alerts duplicate to both systems, and gradually flip traffic after verifying mappings. Archive historical incidents in a searchable format to preserve post-incident reviews.
Which metrics should drive the choice of incident management platform?
Key metrics: mean time to acknowledge (MTTA), mean time to resolve (MTTR), alert volume per incident, number of wake-ups per engineer, and time spent on post-incident actions. Choose tools that improve these operational metrics, not just add features.
How to handle alert fatigue when switching platforms?
Start with stricter deduplication and grouping rules, enable rate-limiting on noisy sources, create temporary suppression windows for maintenance, and iterate rules based on on-call feedback during the pilot.
Are open-source Opsgenie alternatives viable for production?
Open-source solutions can be suitable if the organization has capacity for ongoing maintenance and integration work. They offer customization and cost control at the expense of operational overhead and vendor support.