Cloud Automation Tools: 6 Top Options for IT Infrastructure and How to Choose
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Why compare cloud automation tools for IT infrastructure?
Cloud automation tools help teams provision resources, deploy applications, and enforce policies consistently across environments. Choosing the right set of cloud automation tools affects uptime, deployment speed, compliance, and operational cost. This guide compares six powerful options, explains real trade-offs, and provides a practical S3 Framework checklist to decide which tools fit a given IT infrastructure.
Detected intent: Commercial Investigation
- Primary focus: compare capabilities, trade-offs, and use cases for top cloud automation tools.
- Includes a named decision framework (S3 Framework), a real-world scenario, and 3–5 practical tips.
- Core cluster questions at the end for internal linking and further research.
Top 6 Cloud Automation Tools for IT Infrastructure
These cloud automation tools cover common infrastructure automation needs: infrastructure as code (IaC), configuration management, orchestration, and CI/CD integration. The short summaries highlight strengths and trade-offs so teams can match tools to operational goals.
1. Terraform (Infrastructure as Code)
Terraform uses declarative configuration to provision cloud and on-prem resources across providers. Strengths include provider ecosystem, state management, and modular reuse. Trade-offs: state file management needs discipline and multi-team workflows require locking and remote state backends.
2. Ansible (Configuration Management & Orchestration)
Ansible excels at configuration tasks and ad-hoc orchestration with agentless SSH/WinRM. Strengths: simplicity, readable YAML playbooks, and easy integration with CI/CD. Trade-offs: for large-scale cloud provisioning, combining Ansible with an IaC tool like Terraform is common.
3. Kubernetes + Operators (Container Orchestration & Automation)
Kubernetes automates container scheduling and lifecycle; Operators extend automation to manage stateful workloads and custom resources. Strengths: powerful platform for cloud-native applications and self-healing. Trade-offs: operational complexity and steep learning curve for cluster management and operator development.
4. AWS CloudFormation / Azure Resource Manager / Google Deployment Manager (Provider-Native IaC)
Provider-native templates map directly to cloud services and often provide first-class support for new features. Strengths: tight integration and provider-level feature parity. Trade-offs: vendor lock-in and divergent template languages across clouds, leading teams to prefer multi-provider IaC like Terraform when portability matters.
5. Pulumi (Code-First IaC)
Pulumi allows defining infrastructure with general-purpose programming languages. Strengths: expressiveness, reuse of language constructs, and strong SDKs. Trade-offs: introduces programmer workflows for infrastructure and potential for imperative patterns that reduce predictability if not disciplined.
6. GitOps Tools (Argo CD, Flux) for Declarative Delivery
GitOps tools reconcile Git as the single source of truth with cluster state, enabling automated, auditable deployments. Strengths: drift detection, easy rollbacks, and clear audit trails. Trade-offs: requires a disciplined Git branching and secret management strategy to avoid operational friction.
How to choose: the S3 Framework checklist
Decision-makers benefit from a compact, repeatable checklist. The S3 Framework focuses selection on three priorities:
- Standardize — Can the tool standardize resources and workflows across teams and clouds?
- Secure — Does it support secret management, role-based access control, and policy enforcement?
- Scale — Will the tool handle growth in resources, teams, and deployment frequency without excessive operational overhead?
Apply the S3 Framework by scoring each candidate tool on Standardize, Secure, and Scale (0–5). Choose the tool with the highest combined value that meets the organization’s must-have constraints.
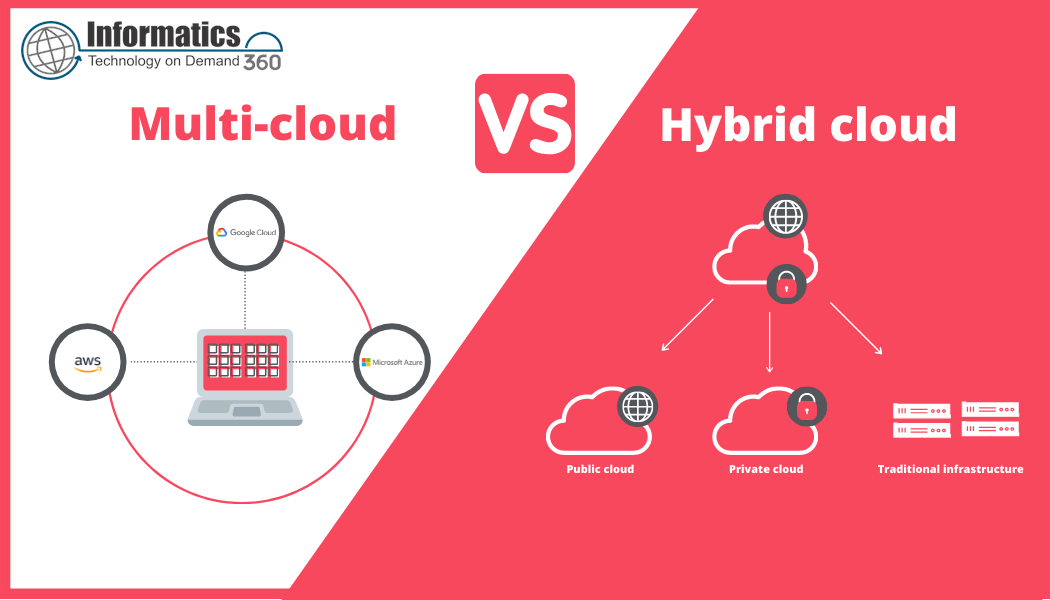
Real-world example: Multi-team rollout for a hybrid cloud
Scenario: A mid-sized company needs a repeatable method to provision networking, Kubernetes clusters on both a public cloud and on-prem, and to deploy microservices. Using Terraform to define provider-agnostic infrastructure, Ansible for bootstrap configuration, and Argo CD for GitOps delivery provides a clear separation: Terraform for lifecycle, Ansible for system configuration, and GitOps for application delivery. This combination follows the S3 Framework: standardized templates, secrets in a vault integrated with RBAC, and scaling through modular modules and GitOps automation.
Trade-offs and common mistakes when selecting cloud automation tools
Picking a tool without assessing organizational capabilities is a frequent error. Common mistakes include:
- Choosing based solely on feature lists rather than team skills and support model.
- Overlooking secret management and assuming built-in solutions are sufficient for compliance.
- Mixing imperative and declarative approaches without defined guardrails, which causes drift and unpredictability.
Trade-offs often center on portability vs. integration. Provider-native IaC gives feature timeliness but reduces portability. Code-first IaC increases expressiveness but can introduce complexity. GitOps improves auditability but requires strict Git workflows.
Practical tips for implementing cloud automation tools
- Start with a minimal, versioned baseline: store templates, modules, and playbooks in Git and enforce pull-request reviews.
- Centralize state and secrets: use remote state backends and a secrets manager with fine-grained access control to prevent leakage and inconsistency.
- Define policies as code early: integrate policy checks (e.g., Open Policy Agent or provider policy tools) into pipelines to prevent misconfigurations at deploy time.
- Automate safe rollbacks: configure deployment tooling so that failures automatically revert to the last known good state or pause for manual intervention.
- Invest in observability: collect metrics from automation workflows (duration, failure rates) to find bottlenecks and improve reliability.
Standards and best practices
Automating infrastructure should follow established security and architecture guidance. Refer to standards and research from recognized institutions for baseline controls and cloud architecture patterns. For example, official guidance on cloud architecture and risk management is published by NIST, which provides a framework for secure cloud deployments. NIST: Cloud Computing
Core cluster questions (use as internal links or future articles)
- How to design an infrastructure-as-code pipeline for multi-cloud deployments?
- What are the security best practices for secret management in automation workflows?
- How to measure ROI when adopting a cloud automation tool?
- What patterns prevent configuration drift with declarative automation?
- How to integrate GitOps with legacy CI/CD systems?
FAQ
What are the best cloud automation tools for IT infrastructure?
Best depends on requirements: Terraform and Pulumi excel for multi-cloud IaC, provider-native templates are best for deep provider integration, Ansible is strong for configuration tasks, Kubernetes and Operators automate container workloads, and GitOps tools provide declarative delivery. Combine tools where each addresses a distinct layer (provisioning, configuration, delivery).
How do cloud orchestration platforms differ from infrastructure automation tools?
Cloud orchestration platforms (like Kubernetes + operators) manage runtime and lifecycle of applications, focusing on scheduling and self-healing. Infrastructure automation tools (IaC, configuration management) focus on provisioning and configuring the underlying resources. Both are complementary: IaC creates clusters; orchestration runs workloads inside them.
How to evaluate infrastructure automation tools for compliance and security?
Evaluate support for policy-as-code, integration with secret stores, RBAC, audit logging, and whether the tool can enforce constraints before deployment. Include compliance checks in CI/CD and use a centralized policy engine to block non-compliant changes.
Can small teams use the same cloud automation tools as large enterprises?
Yes. Small teams should prioritize simplicity and maintainability: choose tools that match team skills, automate repetitive tasks, and avoid over-architecting. Open-source tools often scale well with proper governance and staged adoption plans.
How to migrate from scripts to modern cloud automation tools?
Inventory current scripts and their scope, start by turning repeatable provisioning into declarative templates or modules, migrate secrets to a manager, and introduce CI/CD for automated validation. Apply the S3 Framework to ensure changes standardize workflows, secure secrets and policies, and scale with organizational growth.