Chrome Built-in DNS Tool (2025): Practical Guide, Debugging Steps, and Checklist
Get a free topical map and start building content authority today.
Detected intent: Informational
The Chrome built-in DNS tool is a diagnostic feature inside modern Chromium-based browsers that helps inspect DNS resolution, caching behavior, and DoH/DoT configuration. This guide explains what the tool shows, when to use it, and step-by-step checks to diagnose common DNS issues in 2025.
- Use the Chrome built-in DNS tool to view DNS lookup details, cache entries, and secure DNS settings.
- Follow the DNS Quick-Check Framework for structured troubleshooting.
- Apply practical tips: clear cache, test alternate resolvers, capture a timeline, and verify DoH/DoT behavior.
Understand the Chrome built-in DNS tool
The tool exposes resolution paths (system vs. secure DNS), cache entries, and timing information that are otherwise invisible to browsing users. It is useful for web developers, site operators, help-desk teams, and privacy-conscious users who need to confirm whether browsers are honoring DNS settings or falling back to system resolvers.
What the tool reports and why it matters
The Chrome DNS internals tool typically shows:
- Cached DNS records and TTLs
- Recent resolution attempts and their latency
- Which resolver was used (system resolver, configured DoH provider, or fallback)
- Error codes and reasons for failures (NXDOMAIN, SERVFAIL, timeouts)
These details matter because DNS problems produce a wide range of symptoms — slow page loads, mixed secure/insecure content, or failed connections — and the tool narrows down whether the issue is network, resolver, or cache-related.
When to open the DNS internals view
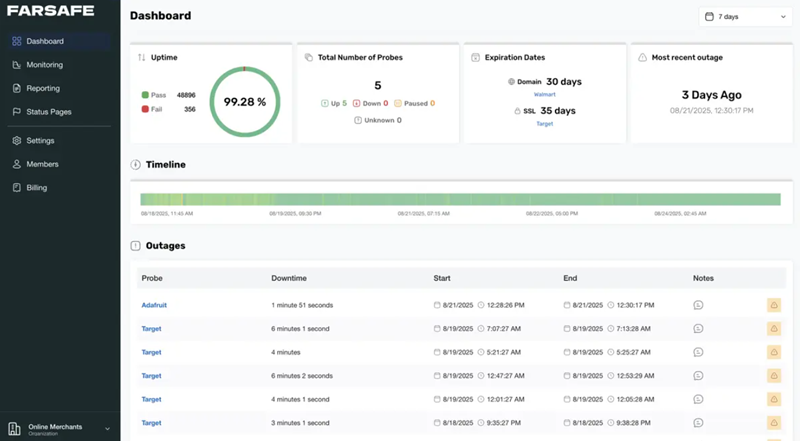
- After a reported website outage or intermittent connection failures.
- When pages load slowly despite normal network throughput.
- To confirm secure DNS (DoH/DoT) enforcement or to debug privacy-related settings.
DNS Quick-Check Framework (named checklist)
Use the DNS Quick-Check Framework to structure investigation: GITV — Gather, Inspect, Test, Validate.
- Gather: Collect client environment details (OS, browser version, network type, configured DoH provider).
- Inspect: Open the Chrome built-in DNS tool and note cache entries, errors, and resolver selection.
- Test: Run controlled tests (clear cache, force reload, switch resolvers) and measure results.
- Validate: Confirm fixes across multiple pages and timelines and document findings for future incidents.
Step-by-step: Troubleshoot with the Chrome built-in DNS tool
Step 1 — Open the DNS internals view
In Chromium-based browsers, open the internal page for DNS diagnostics (for example by navigating to the browser's internal diagnostics URL). The tool lists recent lookups and cache contents. This is the starting point for live inspection.
Step 2 — Inspect cache and recent lookups
Look for cached A/AAAA/CNAME records and their remaining TTL. A stale cache or wrong entry can cause routing to old IPs. If TTLs are unexpectedly long, consider cache flushes or client policy changes.
Step 3 — Run targeted tests
Clear the browser DNS cache, trigger a hard reload, and observe the new lookup. If resolution now succeeds, the issue was a cache or DNS poisoning event. If failures persist, test an alternate resolver or capture the packet timeline.
Step 4 — Validate resolver and security settings
Confirm whether secure DNS (DoH) is active and which provider was chosen. If the browser is falling back to the system resolver unexpectedly, inspect policy and network settings.
Practical tips — quick actions that yield results
- Clear the browser DNS cache, then reload the page to force a fresh lookup.
- Temporarily switch to a known-good resolver (for testing only) to isolate resolver-specific issues.
- Use network capture tools to correlate DNS queries with TCP/HTTPS connection attempts for end-to-end troubleshooting.
- Document the timestamps of failures; many resolvers expose request IDs that help cross-reference logs.
Common mistakes and trade-offs
Common mistakes
- Assuming a browser restart is equivalent to a DNS cache clear — some caches persist beyond restarts depending on platform.
- Overlooking DoH/DoT fallbacks — secure DNS settings can differ from system settings and cause unexpected resolver selection.
- Failing to test from multiple networks — mobile carrier DNS and corporate VPNs often change behavior.
Trade-offs to consider
Enabling secure DNS (DoH/DoT) can improve privacy but may route queries to a provider outside the local administrative domain, complicating internal DNS resolution for private zones. Testing with an alternate resolver is a practical trade-off for isolation, but long-term changes should consider policy and compliance requirements.
Real-world scenario: A public site intermittently unreachable
A website intermittently returns NXDOMAIN for a subset of users. Using the Chrome built-in DNS tool, the following sequence is used: check recent lookups, find NXDOMAIN entries, verify whether the browser used the configured DoH provider, clear the cache, and repeat. The investigation reveals a misconfigured authoritative DNS TTL combined with a caching resolver returning stale NXDOMAIN; switching to a resolver that respected the authoritative TTL fixed user experience while the origin DNS records were corrected.
Related resources and standards
For authoritative DNS protocol details and best practices, consult the IETF publications on DNS behavior and standards: IETF RFC 1035 (DNS).
Core cluster questions for internal linking
- How does a browser choose between system DNS and secure DNS providers?
- What steps show whether DoH is active in a Chromium-based browser?
- How to interpret DNS cache TTLs and when to force a cache clear?
- What diagnostic data should be captured when a website intermittently fails DNS resolution?
- How to test DNS issues across different networks (home, mobile, corporate VPN)?
Closing recommendations
Treat the Chrome built-in DNS tool as an early diagnostic step: use it to collect evidence, then escalate to network traces or resolver logs if needed. Keep a short incident log with timestamps and the actions from the DNS Quick-Check Framework to reduce repeat incidents.
Further reading and continuing practice
Regularly validate resolver behavior as browser updates and OS changes can modify secure DNS behavior. Incorporate DNS checks into routine site monitoring so issues are caught before users report them.
What is the Chrome built-in DNS tool and how is it used?
The Chrome built-in DNS tool displays browser-level DNS lookups, cache entries, resolver selection, and timing. Use it to inspect failed resolutions, confirm DoH/DoT usage, and verify whether the browser is using the expected resolver.
How does secure DNS (DoH/DoT) affect resolution behavior?
Secure DNS encrypts queries and can change which resolver is contacted. This provides privacy but may bypass local DNS configurations, which can affect access to private hostnames or internal zones.
When should the DNS cache be cleared versus switching resolvers?
Clear the browser DNS cache when suspecting stale or poisoned entries. Switch resolvers to isolate whether the issue is resolver-specific. Avoid persistent resolver changes without policy review.
What diagnostic artifacts are most helpful for escalation?
Provide timestamped browser DNS logs, packet captures showing query/response pairs, resolver IP addresses, and evidence of DoH/DoT usage when escalating to network or resolver administrators.
Can DNS issues be caused by browser extensions or local security software?
Yes. Extensions or local security tools that intercept or redirect DNS queries can introduce failures. Test in a clean profile or with extensions disabled to eliminate these variables.