Practical Strategies for Deploying Azure DevOps at Scale
Get a free topical map and start building content authority today.
Deploying Azure DevOps successfully requires a clear plan that balances pipeline automation, security controls, and team governance. This article describes practical tactics for Deploying Azure DevOps across environments, covering CI/CD pipelines, infrastructure as code, governance, security, and operational monitoring.
- Plan a phased rollout that includes pilots, templates, and platform standards.
- Use pipeline-as-code, reusable templates, and agent pool design for scale.
- Apply role-based access control (RBAC), service connections, and secrets management to reduce risk.
- Automate infrastructure using IaC (ARM, Bicep, Terraform) and align with compliance frameworks.
- Implement monitoring, cost controls, and lifecycle policies for long-term maintenance.
Key principles for Deploying Azure DevOps
Successful deployments rely on repeatability, least-privilege security, and observability. Repeatability comes from pipeline-as-code and reusable templates; least-privilege is enforced through RBAC and scoped service connections; observability is achieved via integrated logging and metrics that feed incident workflows. Aligning these principles with organizational policies and regulatory requirements such as ISO 27001, SOC 2, or NIST guidance helps demonstrate compliance and reduce audit overhead.
Design and planning
Define use cases and success criteria
Identify which teams and workloads will move first, the target environments (dev, test, prod), and measurable success criteria such as deployment frequency, mean time to recover (MTTR), and lead time for changes. Include stakeholders from security, operations, and development to ensure cross-functional requirements are met.
Choose a rollout strategy
Common patterns include a central platform team that provides baseline pipelines and templates, followed by a federated adoption by application teams. A phased approach—pilot, expand, and optimize—reduces risk and creates reusable artifacts for later waves.
CI/CD pipelines and automation
Pipeline-as-code and templates
Store pipeline definitions in source control using YAML to version pipeline changes and enable code review. Build shared pipeline templates for common tasks (build, test, package, deploy) to reduce duplication and accelerate onboarding.
Agent pools and scaling
Design agent pools to isolate workloads by sensitivity or resource needs. Use hosted agents for lower-friction builds and self-hosted agents for customized tooling, large artifacts, or network-restricted environments. Consider autoscaling agents for cost efficiency and predictable throughput.
Infrastructure as code and environment management
Use IaC for environments
Provision resources with Infrastructure as Code (IaC) tools such as ARM/Bicep or Terraform. IaC enables repeatable environment creation, drift detection, and integrated deployments. Version and test IaC templates alongside application code and create approval gates for production changes.
Environment isolation and promotion
Maintain separate subscriptions or accounts for production and non-production where appropriate. Implement deployment pipelines that promote artifacts through environments with automated tests, security scans, and manual approvals as required.
Security, secrets, and compliance
Manage identities and access
Apply RBAC to limit permissions, and use groups to manage access consistently. Avoid using shared service accounts; prefer managed identities or service principals with minimal scope and just-in-time approvals when available.
Secure secrets and connections
Keep secrets out of repositories. Use secure stores or key vaults for connection strings and certificates. Integrate secret management with pipelines so secrets are injected at runtime and not persisted in logs.
Testing, quality, and observability
Shift-left testing and automated quality gates
Implement unit, integration, and security scans as early pipeline stages. Use quality gates to prevent low-quality artifacts from progressing. Integrate static analysis, dependency vulnerability checks, and license compliance scans.
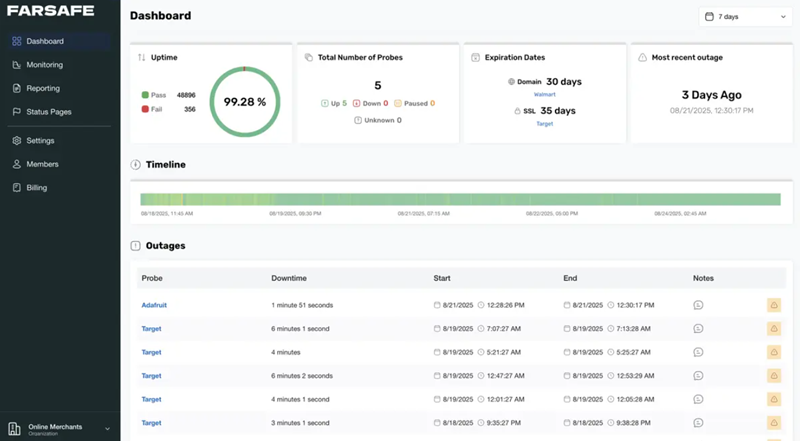
Monitoring, logging, and telemetry
Collect pipeline telemetry, deployment logs, and runtime metrics. Connect alerts to incident management to shorten MTTR. Track deployment success rates, test flakiness, and resource usage so the platform team can optimize templates and agents.
Governance, cost control, and lifecycle
Policy and guardrails
Establish policies for repository structure, branch strategy, naming conventions, and artifact retention. Enforce guardrails through policies and automated checks to maintain platform consistency and reduce the cognitive load for application teams.
Cost management and resource lifecycle
Track pipeline and infrastructure costs. Use quotas, reserved capacity, and autoscaling to manage spend. Implement lifecycle policies to archive or delete stale artifacts and unused resources.
Operational runbook and training
Runbooks and incident playbooks
Create runbooks for common maintenance tasks and clear incident playbooks for deployment failures. Document rollback procedures, hotfix workflows, and escalation paths so teams can respond consistently.
Training and onboarding
Provide bootcamps, templates, and example repositories to accelerate team adoption. Maintain a public platform catalog and FAQs so teams can self-serve common needs with minimal platform team intervention.
Further reading and standards
Refer to official product documentation and platform security guidance for the latest configuration options and compliance features. Microsoft maintains documentation and deployment guides for Azure DevOps that provide implementation details and examples: Microsoft Azure DevOps documentation. Also consider cross-referencing security frameworks such as NIST and ISO when defining control baselines.
FAQ
What are the best practices for Deploying Azure DevOps?
Best practices include using pipeline-as-code, enforcing RBAC, automating infrastructure with IaC, applying security scans early, and rolling out via a phased pilot approach. Implement reuse through templates and maintain observability to measure and improve platform performance.
How should secrets be handled in pipelines?
Secrets should be stored in a secure secret store and referenced by pipelines at runtime. Avoid committing secrets to source control. Use scoped service principals or managed identities and restrict access through least-privilege RBAC.
When is it appropriate to use self-hosted agents instead of hosted agents?
Self-hosted agents are appropriate for builds requiring custom toolchains, access to private networks, large artifact caches, or specific hardware. Hosted agents are suitable for general workloads and reduce maintenance overhead.
How can compliance be supported during deployment?
Map platform controls to compliance requirements, use auditable pipelines, enforce policy as code, and enable logging and retention aligned with regulatory guidance. Consult organizational compliance officers to align technical controls with the required frameworks.
What metrics should be tracked to measure deployment success?
Key metrics include deployment frequency, deployment success rate, mean time to recover (MTTR), lead time for changes, test pass rate, and pipeline resource utilization. These metrics indicate both platform health and organizational delivery performance.