VLANs, Subnets & VTP Explained: Practical Guide to Network Segmentation
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Network segmentation relies on several interrelated technologies. This article explains VLANs, Subnets, and VTP and how they interact in common Layer 2 and Layer 3 designs. The goal is to give a practical, stable reference that helps with design, configuration patterns, and troubleshooting concepts.
- VLANs (Virtual LANs) partition a Layer 2 network into isolated broadcast domains.
- Subnets and IP addressing operate at Layer 3 and map to VLANs for inter-VLAN routing.
- VTP (VLAN Trunking Protocol) is a vendor-specific mechanism to distribute VLAN information across switches; use with caution and follow best practices.
- Trunk ports, 802.1Q tagging, and an appropriate routing architecture are essential for reliable segmentation and security.
VLANs, Subnets, and VTP: Core Concepts
What is a VLAN?
A Virtual LAN (VLAN) separates devices on the same physical switch into different logical Layer 2 networks. Each VLAN forms its own broadcast domain so broadcast and multicast traffic are contained. Switch ports are typically set as access ports (assigned to a single VLAN) or trunk ports (carry multiple VLANs).
How subnets relate to VLANs
A subnet is an IP address range with a network prefix defined by a mask or CIDR notation. In typical designs, each VLAN is associated with one IP subnet. Devices in the same VLAN use the same subnet; communication between VLANs requires a Layer 3 device (router or multilayer switch) to perform inter-VLAN routing.
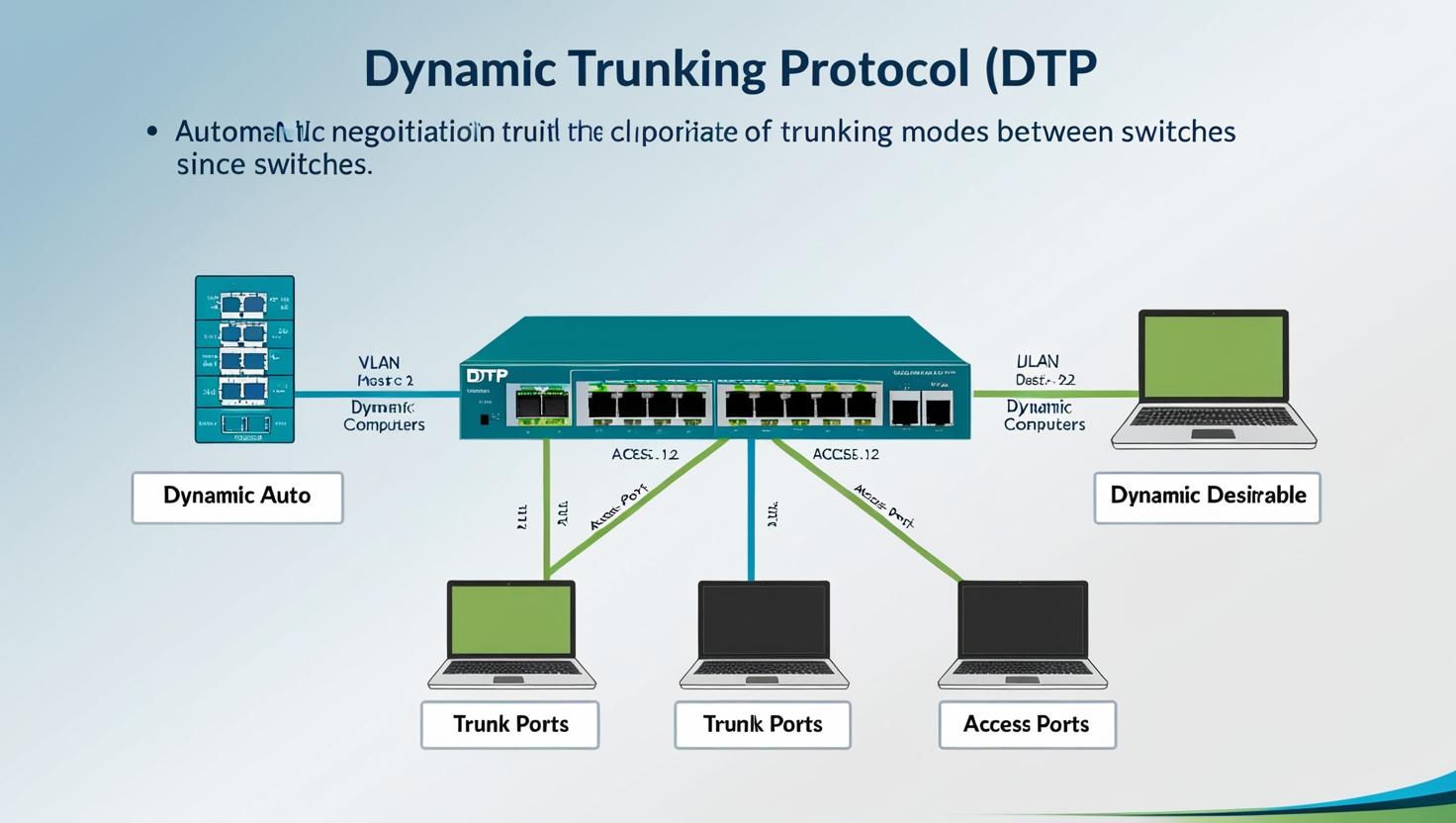
Overview of VTP
VLAN Trunking Protocol (VTP) automates propagation of VLAN configuration across switches in the same VTP domain. It can simplify managing many switches but carries risk: incorrect VTP updates can overwrite VLAN databases, causing outages. VTP modes, pruning, and password features affect behavior. Because VTP is vendor-specific, consider vendor documentation and compatibility when deploying.
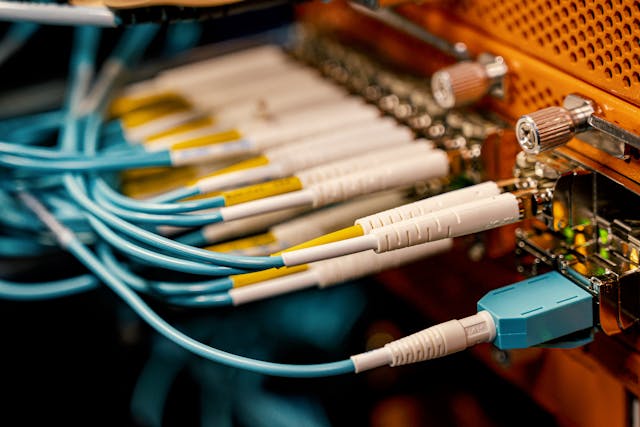
VLANs: Tagging, Trunks, and Port Types
802.1Q tagging
IEEE 802.1Q is the common standard for VLAN tagging on Ethernet frames. A tag inserted into the Ethernet header identifies the VLAN ID (VID). Trunk links carry multiple VLANs using 802.1Q tags while access ports send untagged frames for a single VLAN.
Access and trunk ports
Access ports are assigned to one VLAN and do not tag frames. Trunk ports connect switches or connect to routers and carry multiple VLANs. Configure native VLANs carefully, because native (untagged) traffic can be a security and interoperability concern.
Subnetting and Inter-VLAN Routing
IP addressing and masks
Assign each VLAN a unique IP subnet to avoid routing ambiguity. Use CIDR (Classless Inter-Domain Routing) to control host density. RFC 1918 private address space is commonly used for internal VLANs; public addressing is only needed for devices that must be reachable from the public Internet.
Inter-VLAN routing options
Routing between VLANs can be performed by a Layer 3 switch (using SVI — switched virtual interfaces) or by a dedicated router connected via trunk or routed links. When using a router-on-a-stick, a single physical interface is subinterface-tagged to carry multiple VLANs. For high performance and scale, Layer 3 switching is often preferred.
VTP: Benefits and Risks
When VTP helps
In environments with many switches and frequent VLAN changes, VTP can reduce administrative overhead by distributing VLAN additions and deletions. VTP can also synchronize VLAN configuration across a domain automatically when used correctly.
Common VTP risks and mitigations
Because VTP can propagate changes that remove VLANs, a misconfigured or replacement switch can unintentionally erase the VLAN database. To reduce risk, use version control, VTP domain passwords, and consider setting most switches to VTP transparent mode so they do not accept domain updates. Vendor documentation and support channels provide recommended deployment patterns.
Best Practices and Security Considerations
Design and documentation
Map VLAN IDs to subnets and document their purpose. Keep routing paths simple, minimize spanning-tree complexity, and use consistent naming and VLAN number allocation to avoid confusion. Validate designs with network diagrams and change control.
Hardening VLANs and trunks
Disable unused ports, set unused ports to an unused VLAN and administratively down where possible, and avoid using default VLANs for sensitive traffic. Use port security features, BPDU guard, and other control-plane protections. Monitor for unexpected VLANs or trunking events and apply access control lists (ACLs) at Layer 3 where appropriate.
Troubleshooting Tips
Common faults to check
- VLAN membership mismatches on access ports.
- Trunk negotiation failures or native VLAN mismatches.
- Incorrect IP addressing or duplicate subnets across VLANs.
- VTP version or domain mismatches causing inconsistent VLAN databases.
Useful troubleshooting steps
Verify VLAN and port configuration, check 802.1Q tags with packet captures if necessary, confirm SVI or router interfaces and routes, and inspect VTP status if used. Keep backups of switch configuration and VLAN databases before making changes.
References and Further Reading
Standards and recommendations from IEEE and the IETF provide formal context for VLAN and IP design; vendor documentation explains protocol-specific behavior such as VTP. For vendor-specific VTP guidance, see the official documentation: Vendor VTP documentation.
Final notes
Combining VLANs, subnets, and optional distribution mechanisms such as VTP enables scalable network segmentation when applied with clear design rules and safeguards. Use explicit documentation, cautious automation, and monitoring to reduce the risk that automation introduces outages.
FAQ
What are the main differences between VLANs, Subnets, and VTP?
VLANs are Layer 2 broadcast domains implemented on switches. Subnets are Layer 3 IP networks that are typically mapped one-to-one to VLANs for addressing and routing. VTP is a vendor-specific protocol used to share VLAN configuration across switches automatically; it does not handle IP addressing or routing.
Do VLANs require their own subnet?
In most designs, each VLAN is assigned a unique IP subnet to avoid routing ambiguity. Exceptions exist for special bridging scenarios, but one-subnet-per-VLAN is a recommended practice for predictable routing and security.
Is VTP safe to use in production networks?
VTP can be useful, but it has risks: an incorrect VTP update can overwrite VLAN configuration. Use VTP domain passwords, limit who can be a server, or set switches to transparent mode to avoid unintended propagation of changes. Follow vendor guidance and change control procedures.
How does inter-VLAN routing work?
Inter-VLAN routing requires a Layer 3 device. Options include Layer 3 switches (using SVIs), a router with subinterfaces (router-on-a-stick), or dedicated routed links between routers and switches. The router performs packet forwarding between subnets according to routing tables and ACLs.
How can network segmentation improve security?
Segmentation limits broadcast domains and contains lateral movement by restricting which devices can communicate directly. Combine VLAN segmentation with ACLs, firewalls, and monitoring to enforce security policies and detect anomalies.