Hybrid Cloud in Canada: Control and Agility with a Practical Adoption Checklist
Get a free topical map and start building content authority today.
Detected intent: Informational
Adopting hybrid cloud in Canada offers a pragmatic path to combine the control of private infrastructure with the agility of public cloud services. Organizations that need data residency, regulatory compliance, and predictable performance can still take advantage of elastic compute and modern platform services by using a hybrid approach.
- Hybrid cloud in Canada mixes on-premises or private cloud with public cloud to meet data residency and performance needs.
- Key benefits: data control, compliance alignment (PIPEDA), cost optimization, and workload portability.
- Use the CAN-Hybrid Adoption Checklist to assess readiness, security, network design, and governance.
hybrid cloud in Canada: what it means and why it matters
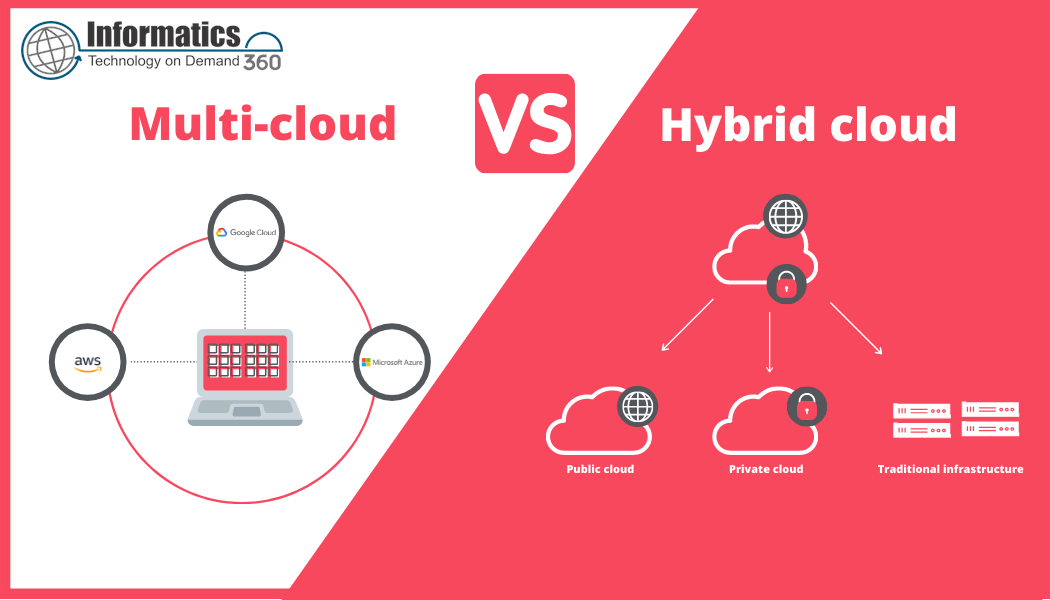
Hybrid cloud in Canada refers to an architecture where workloads run across private infrastructure (on-premises or private cloud) and one or more public cloud environments while maintaining unified operations, security, and governance. This model is useful where data sovereignty, regulatory controls, and latency requirements overlap with demands for elasticity, DevOps velocity, and managed platform services.
Core advantages: control, compliance, and agility
Adopting a hybrid cloud approach brings several concrete benefits:
- Data residency and compliance: Keep sensitive records on-premises or in Canadian-hosted private clouds to meet PIPEDA and provincial rules.
- Operational control: Retain full control over critical systems, encryption keys, and change windows.
- Elastic capacity: Use public cloud for burst compute, analytics, and SaaS platforms without permanently expanding capital infrastructure.
- Performance and latency: Place latency-sensitive services near users—edge computing and local private clouds help.
Design considerations and related terms
When planning hybrid deployments, address these concepts and technologies: private cloud, public cloud, multi-cloud, on-premises virtualization, container orchestration (Kubernetes), IaaS/PaaS/SaaS, software-defined networking (SDN), encryption and key management, identity federation (SAML, OIDC), and edge computing. Also account for cost models, observability, and disaster recovery.
CAN-Hybrid Adoption Checklist (named framework)
An actionable checklist helps avoid common gaps. Use this CAN-Hybrid Adoption Checklist as a practical framework:
- C — Compliance & Data Residency: Map data classes, residency requirements, and retention rules. Assign where data must reside.
- A — Architecture & Connectivity: Define network topology, VPN/Direct Connect designs, and latency targets between environments.
- N — Network Security & Identity: Implement segmentation, zero-trust controls, centralized identity, and key management.
- Deployment & Operations: CI/CD pipelines, infrastructure as code (IaC), and unified monitoring must span both clouds.
- Governance & Finance: Tagging, cost allocation, and change control. Set guardrails for public cloud usage and service procurement.
Real-world example
A mid-sized Canadian fintech keeps customer account data in a private cloud hosted within Canada to meet PIPEDA requirements and reduce audit scope. Non-sensitive workloads—batch analytics, model training, and a customer-facing mobile API—burst to a public cloud for overnight processing. Secure connectivity uses a dedicated link with IAM federation so developers can use the same identity provider across environments. The result is regulated control for sensitive data and cloud-speed innovation for analytics.
Practical tips for implementation
- Start with a workload map: classify each application by sensitivity, latency needs, and cloud readiness.
- Standardize identity and secrets: centralize IAM and encryption key management to reduce attack surface and simplify audits.
- Use infrastructure as code and shared pipelines so deployments are repeatable across private and public clouds.
- Design for observability: implement centralized logging, tracing, and metrics that correlate across environments.
- Plan for exit and portability: containerize or package workloads to avoid lock-in and simplify disaster recovery.
Common mistakes and trade-offs
Hybrid cloud is not a one-size-fits-all solution. Consider these trade-offs and avoidable errors:
- Overcomplicating architecture: Adding hybrid elements increases operational overhead—start small and iterate.
- Ignoring network constraints: Latency and bandwidth can erode expected performance gains; test under realistic loads.
- Poor governance: Inconsistent tagging, shadow IT, and unmanaged public cloud spend create security and financial risk.
- Assuming identical tooling: Not all services map cleanly between providers—expect integration work for authentication, monitoring, and backup.
Standards, guidance, and compliance context
Design decisions should align with recognized guidance for cloud architectures and definitions. For precise cloud terminology and reference definitions, consult standards such as the NIST cloud computing definition and related publications. The NIST cloud definition clarifies public/private/hybrid distinctions and is a useful technical reference for architecture and compliance discussions: NIST Special Publication 800-145. Also review Treasury Board of Canada Secretariat guidance and provincial privacy authorities for data residency and PIPEDA interpretation.
Core cluster questions
- How does hybrid cloud help meet Canadian data residency requirements?
- What are the cost trade-offs between private infrastructure and public cloud bursts?
- How to design network connectivity for a secure hybrid environment?
- Which governance controls are essential for hybrid cloud operations?
- What workloads are best suited for on-premises versus public cloud in a hybrid model?
Final checklist before committing
Before moving to hybrid, confirm these items:
- Data classification policy and residency mapping are documented and approved.
- Network connectivity and latency SLAs are measurable and validated.
- IAM and key management span environments with centralized logging and alerting.
- Cost model and governance guardrails are in place to prevent runaway spend.
- Disaster recovery and portability tests have been completed for critical applications.
Is hybrid cloud in Canada necessary for data residency compliance?
Not always. Hybrid cloud is one effective pattern to meet data residency and compliance while retaining cloud agility. Some organizations can meet requirements with a single Canadian public cloud provider; others need private infrastructure for specific workloads. The right choice depends on data classification, audit scope, and regulatory interpretation.
How does hybrid cloud address latency and performance issues?
Placing latency-sensitive services on-premises or in local private clouds reduces round-trip times. Edge computing and regional public cloud zones can also help. Design for locality and measure performance under real-world conditions rather than assuming cloud placement will automatically meet latency targets.
What are the security best practices for hybrid cloud?
Use least-privilege identity, centralize key management, apply micro-segmentation, and ensure consistent vulnerability scanning and patching across environments. Adopt a zero-trust mindset and automated compliance checks to maintain a consistent security posture.
How should costs be managed across hybrid environments?
Implement tagging, chargeback or showback models, and budgeting with thresholds. Use cost monitoring tools that can correlate expenses across private and public environments. Forecast burst usage and include network egress when modeling costs.
Can existing legacy applications be migrated into a hybrid model?
Many legacy applications can be adapted incrementally—start with non-critical services or reporting workloads. Modernization approaches include containerization, refactoring to cloud-native services, or keeping apps on-premises and integrating via APIs and messaging layers. Perform a compatibility and risk assessment before migration.