How to Build a Practical Multi-Cloud Strategy: Checklist, Trade-offs, and Best Practices

Get a free topical map and start building content authority today.
A clear multi-cloud strategy guides which workloads run where, what governance is required, and how to manage costs and risk across providers. This article explains practical patterns, a simple readiness checklist, common mistakes to avoid, and a real-world scenario that shows how multiple providers can be used effectively.
Multi-cloud strategy: core concepts and why it matters
At its simplest, a multi-cloud strategy is a formal plan for using two or more cloud providers to achieve specific business outcomes—resilience, cost optimization, regulatory compliance, or access to specialized services. Common patterns include active-active deployments for resilience, best-of-breed selection for specialized services (e.g., AI, analytics), and regional diversification for compliance.
Key drivers for adopting multi-cloud
- Risk reduction: avoid provider lock-in and single-vendor outages.
- Technical fit: choose platforms that match workload requirements (GPU, high-memory, managed databases).
- Regulatory or data residency needs: keep data in required jurisdictions.
- Cost flexibility: exploit competitive pricing or spot inventory.
Common models and trade-offs
Models include active-active, active-passive disaster recovery, and split workloads by function. Trade-offs generally appear between operational complexity and business benefit: more providers mean more integration work, different APIs, and higher skills demand.
Multi-cloud architecture best practices
Design principles
- Define the minimal set of cross-cloud dependencies: use cloud-agnostic formats (containers, Terraform, OCI-compliant images) where possible.
- Use identity and access management as the primary security boundary: centralize authentication with standards like SAML or OIDC and federate provider IAM.
- Automate networking and infrastructure as code to reduce configuration drift and enable reproducible deployments.
- Standardize logging, metrics, and tracing using open formats (OpenTelemetry) to enable cross-cloud observability.
Multi-cloud architecture best practices in action
Implement a central policy and governance layer for security baselines, tagging, and cost allocation. Adopt service meshes or API gateways to normalize cross-cloud service discovery and traffic management. These steps reduce operational friction and improve visibility.
MULTI-CLOUD READY checklist (named framework)
The MULTI-CLOUD READY checklist is a quick readiness framework for teams planning multi-cloud adoption:
- Map: inventory apps, data sensitivity, and latency needs.
- Unify identities: ensure single identity provider or federated IAM.
- Layer policies: define security, compliance, and cost policies centrally.
- Tools: select infrastructure as code and multi-cloud management tools.
- Integrate: design data flows and network routes with clear egress/inbound rules.
- Cost plan: model TCO including egress, cross-cloud transfers, and duplicate capabilities.
- Assess skills: plan training or hiring to cover multiple provider platforms.
- Deploy gradually: start with non-critical workloads and validate operations.
- Recover: test DR and failover procedures across providers.
- Yearly review: revisit provider fit and costs annually.
Practical tips for operating multiple clouds
- Standardize on portable artifacts: container images, Helm charts, and Terraform modules reduce provider-specific work.
- Centralize observability: collect metrics and traces into a platform or standardized data lake for correlation.
- Automate policy enforcement: use policy-as-code (for example, Open Policy Agent) to prevent drift.
- Negotiate contracts around SLAs and data transfer: explicitly include cross-region and egress rates in cost models.
Practical tip: choose multi-cloud management tools carefully
Look for tools that support policy, cost visibility, and lifecycle automation across providers. For specific selections, evaluate supported APIs, role-based access, and integration with existing CI/CD pipelines.
Trade-offs and common mistakes
Common mistakes
- Starting with critical systems: failing to pilot increases outage risk.
- Replicating operators and toolchains per cloud without automation: creates silos and wasted effort.
- Ignoring data transfer costs and latency: cross-cloud traffic can quickly inflate bills and degrade performance.
- No clear rollback or DR plan across providers: complicates incident response.
Trade-offs to consider
Multi-cloud offers flexibility and risk reduction at the cost of higher operational complexity. If the business priority is simplicity and low operational overhead, a single-cloud approach may be preferable. If resilience, compliance, or specialized services are critical, multi-cloud can provide measurable benefits.
Real-world example
Example scenario: an online retailer separates storefront services and analytics. The storefront runs on Provider A for global CDN and managed database capabilities, while heavy analytics workloads run on Provider B for cheaper spot GPU capacity and a specialized analytics service. A federated identity provider handles SSO across accounts, and a central logging pipeline aggregates logs into a cross-cloud data lake for security monitoring. Disaster recovery for the storefront is an active-passive setup configured to failover to Provider C in a different jurisdiction.
For formal definitions and guidance on cloud models and characteristics, refer to NIST's cloud computing program for established concepts and terminology: NIST Cloud Computing Program.
FAQ
What is a multi-cloud strategy and when is it needed?
A multi-cloud strategy is a plan for using multiple cloud providers to meet business goals such as resilience, compliance, or access to specialized services. It is typically needed when risk mitigation, geographic coverage, or provider-specific features are required and justify the operational cost of managing multiple environments.
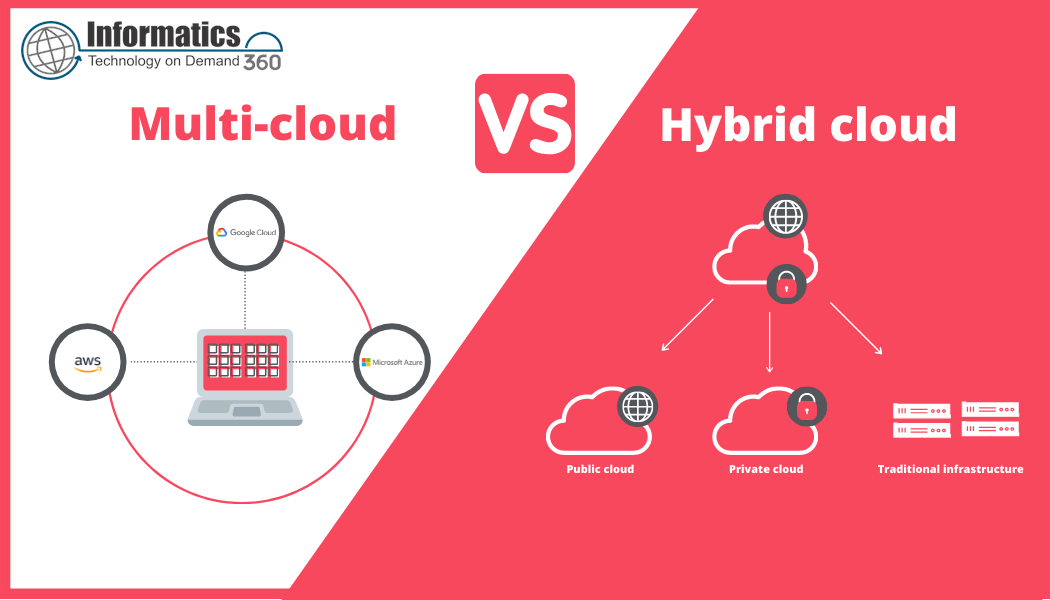
How do multi-cloud and hybrid cloud compare?
Hybrid cloud mixes public cloud(s) with private infrastructure; multi-cloud uses multiple public clouds. Hybrid focuses on workload placement between private and public clouds for control or latency reasons; multi-cloud focuses on distributing workloads across multiple public providers for resilience, cost, or feature access.
Which security controls are essential across clouds?
Essential controls include centralized identity and access management, encryption in transit and at rest, consistent logging and SIEM integration, network segmentation, and policy-as-code to enforce baselines across accounts and regions.
How should costs be tracked across multiple providers?
Implement unified tagging standards, collect billing and usage data into a central cost management tool, and model egress and cross-cloud interactions during the architecture and procurement phases. Regular cost reviews and alerts on abnormal spend are critical.
What are practical first steps to adopt a multi-cloud approach?
Begin with an inventory of applications and dependencies, run a small pilot (non-critical workload), adopt infrastructure-as-code, and set up centralized identity and observability before scaling to production.