AWS Cloud Consulting Cybersecurity: Practical Guide to Strengthening Cloud Security in 2025
Get a free topical map and start building content authority today.
Intent: Informational
Cloud security is no longer just a checklist item; it is a continuous program. This article explains how AWS cloud consulting cybersecurity approaches are changing in 2025, what practical steps organizations should take, and how to evaluate consulting partners or internal programs. The term "AWS cloud consulting cybersecurity" will be used throughout to describe services and practices that combine AWS-native controls, third-party tooling, and governance to reduce cloud risk.
AWS cloud consulting cybersecurity: what consultants change in 2025
Consulting companies focused on AWS have shifted from reactive projects to continuous program delivery. Services now blend architecture reviews, automated posture management, threat hunting, and compliance automation. These firms apply proven standards—such as the NIST Cybersecurity Framework and AWS Well-Architected security pillars—to design repeatable controls. For a reliable reference on frameworks, the NIST Cybersecurity Framework provides core functions and implementation guidance (NIST).
What modern AWS cloud consulting cybersecurity services include
Typical capabilities offered by consulting teams include:
- Identity and access modernization with least-privilege IAM and Zero Trust principles.
- Automated infrastructure posture management using CSPM (Cloud Security Posture Management) and IaC scanning.
- Runtime protection and visibility with CWPP, EDR integration, and container security.
- Log aggregation, SIEM tuning, and managed detection & response (MDR) for cloud workloads.
- Encryption, key management (KMS), and secure secret handling.
- Compliance-as-code and continuous auditing mapped to standards like CIS Benchmarks and industry regulations.
Cloud security consulting best practices and role of automation
Automation is central—manual checklists do not scale. Consultants implement policies as code, automated alerting, and enforcement gates in CI/CD pipelines to reduce drift. This aligns with cloud security consulting best practices such as single-pane visibility, enforcement at build time, and focused blue/ purple team exercises to validate defenses.
5-step CLOUD-SECURE framework (named checklist)
Use the CLOUD-SECURE checklist as a practical framework to evaluate readiness and plan improvements. Each step maps to action items and measurable outcomes.
- Clear responsibilities — document shared responsibility, team roles, and runbooks.
- Leverage least-privilege access — enforce IAM roles, session management, and short-lived credentials.
- Observe continuously — centralize logs, enable CloudTrail, GuardDuty-style detection, and SIEM collection.
- Utilize automation — policy-as-code, IaC scanning, and automated remediation playbooks.
- Defend runtime — implement CWPP, container security, and host protection.
- Secure data — encryption at rest/in transit, key rotation, and data classification.
- Enhance testing — red team, purple team, and recovery drills; ensure DR plans are tested.
Real-world example: mid-size fintech migration
A mid-size fintech migrated customer-facing services to AWS and engaged a consulting firm to secure the environment. The consultant implemented the CLOUD-SECURE checklist: reworked IAM to support role-based access and short-lived credentials, added IaC scanning gates in the CI/CD pipeline, deployed centralized logging and a managed detection solution tuned to financial transaction patterns, and automated compliance evidence collection for audits. Resulting changes lowered mean time to detect (MTTD) through improved telemetry and reduced privileged access risk via enforced least-privilege policies.
Practical tips for in-house teams and procurement
- Start with high-value assets: classify workloads and protect the most sensitive data and APIs first.
- Require security-as-code in procurement: demand IaC scanning reports and deployment-time policy checks.
- Measure security with metrics: track MTTD, MTTR, privilege explosion events, and IaC policy failures.
- Use segmentation: network and identity segmentation reduce blast radius and simplify incident response.
- Run regular tabletop exercises and test backups to verify recovery assumptions.
Trade-offs and common mistakes
Selecting the right trade-offs prevents wasted effort:
- Over-automation vs. pragmatic control: Automating every rule can block developers. Prioritize enforcement on production and high-risk environments; use advisory mode in dev.
- Tool overload: Many tools claim coverage (CSPM, CWPP, SIEM, EDR). Consolidate to reduce alert fatigue and integrate telemetry into one pane.
- Neglecting identity: Identity problems are the root cause of many breaches. Do not treat IAM as an afterthought.
- Compliance copy-paste: Passing an audit does not equal security. Combine compliance automation with threat-hunting and configuration hardening.
Common mistakes to avoid
- Assuming cloud provider defaults are secure—default services often require configuration.
- Delaying encryption and key management until later phases.
- Not mapping controls to business risk—security controls should reduce measurable risk, not just produce more logs.
How to evaluate AWS cloud consulting cybersecurity partners
When assessing providers, verify experience with AWS native controls and modern tooling, request case studies, and require measurable SLAs on detection and response. Ask for evidence of following standards (NIST, CIS Benchmarks) and for runbooks that demonstrate incident playbooks tailored to the environment.
Core cluster questions (for internal linking or topic expansion)
- What are the responsibilities in the AWS shared responsibility model for cloud security?
- How do CSPM and CWPP differ and when are both needed?
- Which IAM and Zero Trust design patterns reduce privilege escalation risk?
- What are best practices for automating compliance checks in CI/CD pipelines?
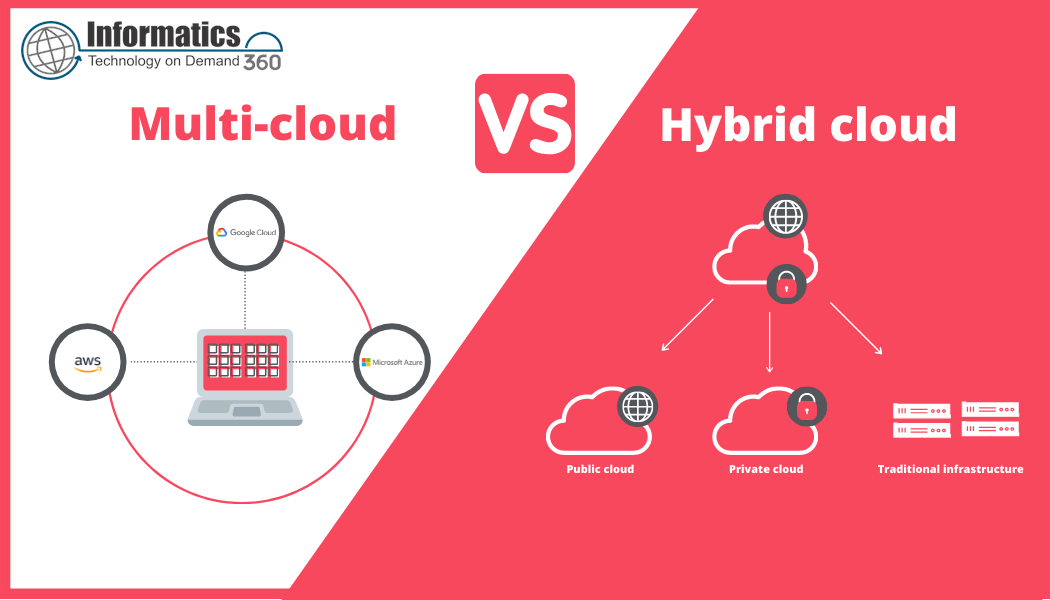
- How should cloud incident response plans be structured for multi-account AWS environments?
Frequently asked questions
What is AWS cloud consulting cybersecurity and why is it important?
AWS cloud consulting cybersecurity describes services that help organizations secure workloads on AWS. It combines architecture, automation, monitoring, and incident response to reduce risk and ensure compliance. It is important because cloud-native controls and rapid change cycles require continuous security governance rather than one-time projects.
When should an organization hire a cloud security consultant versus building in-house?
Engage consultants when specialized skills are needed quickly (migration, incident response, or regulatory projects) or when in-house teams lack operational experience. Consider managed services or co-sourced models when long-term operations need to scale without delaying time-to-market.
How do managed AWS cybersecurity services and internal teams work together?
Managed services can provide 24/7 monitoring and incident response coverage while internal teams retain strategic control over architecture and policy. Integration points include shared runbooks, ticketing systems, and periodic purple-team exercises to transfer knowledge and improve detection rules.
What compliance frameworks should be used for AWS deployments?
Common frameworks include NIST Cybersecurity Framework, ISO 27001, PCI DSS (for payment data), and CIS Benchmarks for configuration hardening. Map controls to regulatory requirements and use automated evidence collection to simplify audits.
How can the CLOUD-SECURE checklist be applied to an ongoing cloud program?
Apply the CLOUD-SECURE steps in iteration: assess responsibilities and identity first, deploy monitoring and automation next, then harden runtime protections and secure data. Use measurable gates for promotion to production and schedule recurring reviews for each step.