Cloud Networking Basics: Practical Guide to Connectivity and Data Flow

Get a free topical map and start building content authority today.
Understanding cloud networking basics is essential for designing reliable, secure, and cost-effective cloud applications. This guide explains common connectivity models, how data flows through cloud environments, design principles, a practical checklist, real-world examples, and common mistakes to avoid.
- Connectivity options include VPCs, peering, VPN, transit gateways, and direct interconnects.
- Data flow depends on routing, NAT, load balancers, and service meshes for microservices.
- Use the CLOUD-ARC checklist to validate connectivity, routing, resilience, and security before launch.
Cloud networking basics: Core concepts and components
Cloud networking basics cover virtual networks (VPC/VNet), subnets, routing tables, network address translation (NAT), security controls (security groups, ACLs, firewalls), and connectivity options such as site-to-cloud VPN, dedicated interconnects, and peering. Key entities and protocols include CIDR addressing, BGP for dynamic routing, DNS, and load balancing. These components determine how packets traverse from users to services and between services inside the cloud.
Connectivity models and when to use them
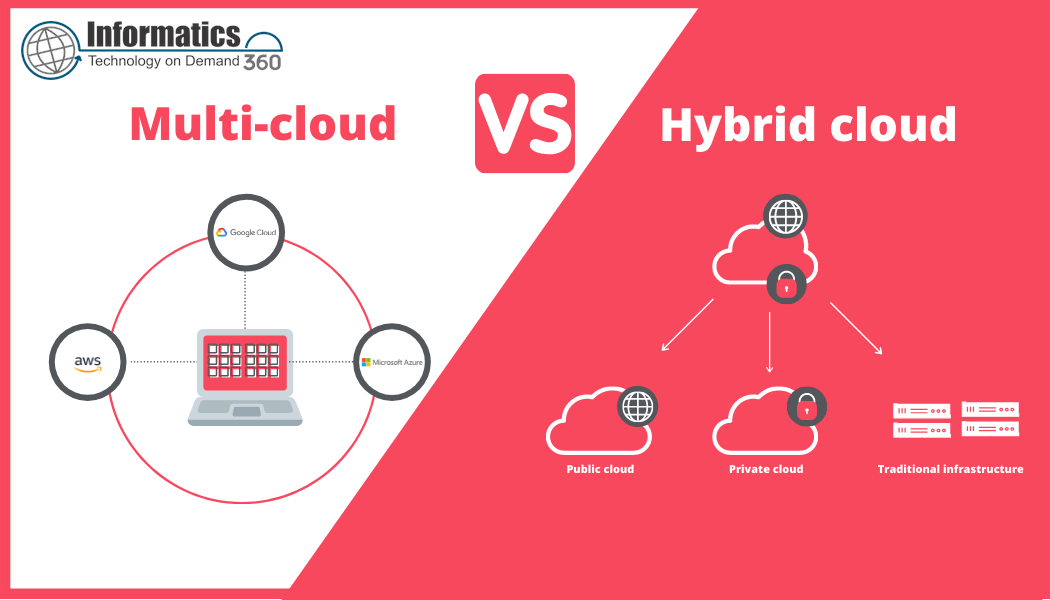
Common cloud connectivity models include:
- VPC/VNet with peering — low-latency intra-cloud connectivity when both environments are in the same provider.
- Transit gateway or hub-and-spoke — centralizes routing for multi-VPC or multi-account setups to simplify management.
- Site-to-cloud VPN — encrypted over internet for branch connectivity; good for small-scale or temporary links.
- Direct interconnect or dedicated link — high-throughput, low-latency private connections for production or data-heavy applications.
Choosing the right model depends on security, latency, throughput, and operational complexity. These cloud connectivity models are commonly supported by major cloud providers and have trade-offs in cost and manageability.
Data flow in cloud networks: How traffic moves
Data flow in cloud networks describes how an incoming request travels from an external client through edge services (CDN, load balancer), into a virtual network, across subnets, and finally to the application instance or storage. Microservices may route internal traffic via a service mesh or sidecar proxies, and east-west traffic often requires explicit routing and security controls. Observability (flow logs, packet captures, metrics) is essential to trace and optimize data flow in cloud networks.
Key elements that affect data flow
- Routing rules and BGP policies — determine path selection between networks and regions.
- NAT and egress controls — translate private addresses and control outbound access.
- Load balancers and ingress controllers — terminate client connections and distribute load.
- Firewall and security groups — enforce allowed traffic patterns and microsegmentation.
CLOUD-ARC Checklist (framework)
Use the CLOUD-ARC Checklist to validate network readiness before deployment:
- Connectivity — Confirm peering, transit, or interconnect links and IP plan (CIDR).
- Latency — Measure RTT between critical services and set SLAs.
- Orchestration — Ensure IaC templates provision consistent routing and security groups.
- Uptime — Plan for multi-az/region failover and redundancy.
- DNS & Discovery — Verify private DNS resolution and service discovery mechanisms.
- Resilience — Implement health checks, retries, and circuit breakers.
- Compliance — Audit logs, encryption in transit, and access controls.
- Cost — Estimate data egress, inter-region transfer, and peering charges.
- Observability — Enable flow logs, VPC logs, and network metrics for troubleshooting.
- Change control — Test routing changes first in staging and review with runbooks.
Real-world example
A multi-tier web application migrates from on-premises to cloud. The architecture uses a hub-and-spoke model: a transit gateway connects three application VPCs, a dedicated interconnect provides high-throughput links to the data center, and NAT gateways handle egress. DNS routing directs traffic through a global load balancer. Health checks and automated failover policies reduce downtime during regional failures. Observability is provided by flow logs and centralized network metrics to detect asymmetric routing and packet loss.
Practical tips for building reliable cloud networks
Actionable points
- Plan a clear IP addressing scheme using non-overlapping CIDR ranges to simplify peering and VPNs.
- Use transit or hub topology for many VPCs to reduce complex peering meshes and centralize inspection.
- Enable flow logs and centralized monitoring before production to capture baseline traffic patterns.
- Test failover paths and maintenance scenarios; automate route propagation with IaC tools.
- Document egress paths and costs to avoid unexpected charges from frequent inter-region traffic.
Common mistakes and trade-offs
Typical errors include overlapping IP ranges during migration, underestimating egress costs, relying solely on VPNs when dedicated interconnect is required for performance, and cluttered peering meshes that grow operational overhead. Trade-offs often involve balancing cost vs. performance: dedicated links reduce latency and jitter but increase fixed costs. Centralized routing simplifies control but can become a bottleneck without proper scaling.
Standards and best practices
Referencing standards bodies helps align architecture with industry practices. The NIST cloud computing definition clarifies core service models and shared responsibilities; for implementation details, industry protocols such as BGP (IETF) govern inter-network routing. For reference on definitions and responsibilities, see the NIST cloud computing definition.
Monitoring and validation
Use active probes (ping, traceroute), synthetic transactions, and packet-level metrics to validate paths. Automate health checks and route verification during CI/CD to prevent configuration drift. Ensure network ACLs and security groups are part of automated tests to avoid accidental wide-open access.
FAQ
What are cloud networking basics that every engineer should know?
Fundamentals include virtual networks (VPC/VNet), subnetting, routing tables, NAT, security groups/firewalls, load balancers, and connectivity choices like VPNs, direct interconnects, peering, and transit gateways. Understanding how these pieces control ingress, egress, and east-west traffic is critical.
How do cloud connectivity models differ in latency and cost?
Site-to-cloud VPNs use the public internet and have variable latency and lower fixed cost. Dedicated interconnects provide consistent low-latency performance but higher fixed costs. Transit gateways add management simplicity but can introduce additional charges; evaluate expected throughput and SLAs when choosing.
When should a transit gateway or hub-and-spoke be used instead of VPC peering?
Choose transit gateway when connecting many VPCs or accounts to avoid n*(n-1)/2 peering relationships. Transit models centralize routing and policy enforcement, easing management for enterprise-scale deployments.
How to secure data flow in cloud networks?
Implement least-privilege security groups, network ACLs for subnet-level filtering, TLS for in-transit encryption, and microsegmentation for workloads. Use centralized monitoring and audit logs to detect misconfigurations or suspicious flows.
What monitoring is required to validate network performance?
Collect flow logs, latency and throughput metrics, packet loss, and application-level health checks. Synthesize transactions from multiple regions to measure real-user experience and correlate with infrastructure metrics to find bottlenecks.