Managing Data Privacy and Security Risks in Cloud Computing
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Data privacy and security in cloud computing are central concerns for organizations that store, process, or transmit information using cloud services. Cloud environments introduce specific risks—such as multi-tenancy exposure, insecure APIs, and complex data residency rules—that affect confidentiality, integrity, and availability of data. Understanding these issues helps organizations assess risk, implement controls, and meet regulatory obligations.
Key data privacy and security challenges in cloud computing
Data breaches and unauthorized access
Data breaches occur when sensitive information is exposed through external attacks, misconfigured storage, or compromised credentials. In cloud contexts, shared infrastructure and APIs increase the attack surface. Unauthorized access can stem from weak identity controls, poor key management, or insufficient segmentation between tenants.
Data loss and availability risks
Data loss may result from accidental deletion, hardware failure, or ransomware. While many cloud services offer redundancy, recovery depends on backup practices, retention policies, and the ability to export data. Business continuity planning and tested recovery procedures are critical to address availability risks.
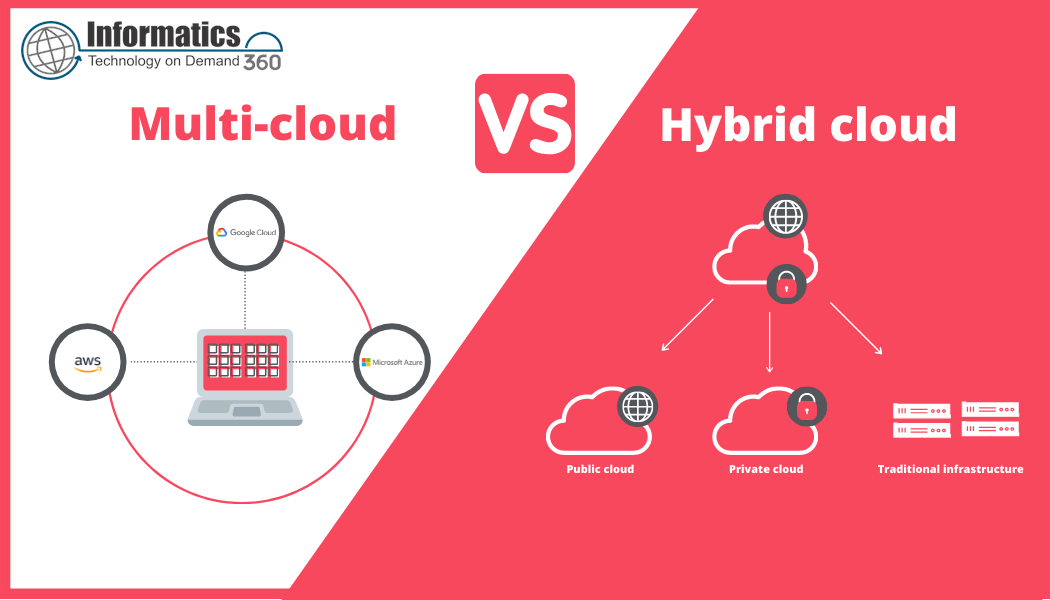
Multi-tenancy and isolation issues
Multi-tenant architectures consolidate resources among multiple customers. Faulty isolation can enable one tenant to affect another. Proper logical and network isolation, hypervisor hardening, and regular vulnerability assessments reduce cross-tenant exposure.
Insecure or misused APIs
Cloud services depend heavily on APIs for management and integration. Insecure APIs, weak authentication, or excessive permissions can enable attackers to manipulate services or exfiltrate data. API security controls and least-privilege design are important defenses.
Compliance, governance, and data residency
Regulatory frameworks—such as the EU General Data Protection Regulation (GDPR), sector rules like health or financial regulations, and national data residency laws—impose requirements on how personal and sensitive data are stored, processed, and transferred. Cloud architectures that span multiple jurisdictions can complicate compliance and require explicit governance and contractual arrangements.
Common technical and organizational controls
Encryption and key management
Encryption of data at rest and in transit reduces the risk of disclosure. Effective key management—who controls keys, how keys are rotated, and where keys are stored—is equally important. Consider separation of duties so that cryptographic keys are managed independently of the data environment when regulatory or contractual obligations require it.
Identity and access management (IAM)
Strong IAM practices—such as multi-factor authentication, role-based access controls, privileged access management, and regular review of permissions—help prevent unauthorized access. Authentication and authorization logs support auditing and incident investigation.
Monitoring, logging, and incident response
Continuous monitoring and centralized logging enable detection of anomalies, suspicious activity, and potential breaches. An incident response plan tailored to cloud scenarios should define roles, notification procedures, forensic data collection, and coordination with cloud service providers.
Configuration management and vulnerability control
Misconfiguration is a frequent cause of cloud incidents. Automated configuration scanning, infrastructure-as-code reviews, patch management, and vulnerability scanning reduce exposure. Regular third-party assessments or penetration tests provide additional assurance.
Contractual safeguards and third-party risk management
Contracts with cloud service providers should address data handling, security responsibilities, breach notification timelines, audit rights, and end-of-contract data return or deletion. A formal vendor risk program helps evaluate provider controls and compliance certifications.
Standards, guidance, and regulatory considerations
Several organizations provide standards and guidance relevant to cloud security and privacy. ISO/IEC 27001 and ISO/IEC 27017 describe information security management and cloud-specific controls. National and regional regulations, such as GDPR, set requirements for processing personal data. The U.S. National Institute of Standards and Technology (NIST) publishes cloud security guidance and special publications that help align technical and governance measures. For further detailed guidance from a recognized standards body, see NIST publications on cloud security: NIST Special Publication 800-144.
Risk assessment and lifecycle management
Data classification and minimization
Inventorying data assets and classifying them by sensitivity guides protection levels. Applying data minimization principles—collecting and retaining only what is necessary—reduces the scope of risk and simplifies compliance.
Data retention and deletion
Clear retention policies and mechanisms for secure deletion at the end of lifecycle or contractual periods are essential. Where regulations require proof of deletion or restricted retention, technical and contractual controls should document compliance.
Shared responsibility and organizational alignment
Cloud deployments operate under a shared responsibility model: providers typically secure underlying infrastructure while customers are responsible for their data, identities, and configurations. Clear internal roles, supplier oversight, and executive-level governance align security, privacy, and legal functions.
Frequently asked questions
What are the main data privacy and security in cloud computing concerns?
Main concerns include unauthorized access, data breaches, misconfiguration, insecure interfaces, cross-border data transfer restrictions, and insufficient controls over encryption and key management. Addressing these concerns requires combined technical, contractual, and governance measures.
How do regulations like GDPR affect cloud use?
Regulations such as GDPR impose obligations on data controllers and processors to protect personal data, document processing activities, and respect data subject rights. When cloud services are used, contracts, data transfer mechanisms, and technical safeguards must reflect these obligations and ensure accountability.
Are certifications enough to prove a cloud provider is secure?
Certifications (for example ISO 27001 or SOC reports) indicate that a provider has implemented assessed controls, but they do not remove the need for customer-side controls, configuration reviews, and ongoing monitoring. Certifications should be one component of a broader assurance program.
What role does encryption play in cloud security?
Encryption protects data confidentiality both in transit and at rest. Effective implementation must include secure key management, appropriate algorithms, and processes for key rotation. Legal and operational requirements may influence whether keys are customer-controlled or managed by the provider.
How should organizations prepare for cloud-related incidents?
Preparation includes maintaining an incident response plan that addresses cloud-specific scenarios, ensuring logging and forensic capabilities, defining escalation and notification procedures, and conducting regular tabletop exercises to validate readiness.