Network Automation Tools: Benefits, Architecture, and Best Practices
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Network automation tools help organizations reduce repetitive tasks, improve consistency, and scale network operations. This article explains what network automation tools do, common architectures and components, implementation approaches, and practical considerations for reliability, security, and compliance.
- Network automation tools automate configuration, provisioning, monitoring, and remediation across devices and services.
- Key technologies include APIs, model-driven management (YANG), telemetry, and orchestration layers such as intent-based systems and SDN controllers.
- Benefits include faster change cycles, fewer errors, improved visibility, and easier compliance reporting.
- Risks include configuration drift, security exposure, and operational complexity; governance, testing, and observability reduce these risks.
What network automation tools do and why they matter
Network automation tools centrally manage tasks such as device configuration, firmware updates, service provisioning, and real-time monitoring. By replacing manual CLI work with repeatable workflows, automation reduces human error and improves consistency across routers, switches, firewalls, and virtual network functions. Automation also enables rapid scaling of services for cloud and distributed architectures and supports modern practices like continuous integration/continuous delivery (CI/CD) for infrastructure.
Core components and technologies
APIs and model-driven management
APIs and data models provide structured access to network devices. Common models use YANG for data modeling and protocol adapters like NETCONF or RESTCONF to read and apply configurations. These standards are developed and published by organizations such as the Internet Engineering Task Force (IETF), which provides protocols and best practices that underpin many automation solutions. For more information about standards and community specifications, see the IETF website: IETF.
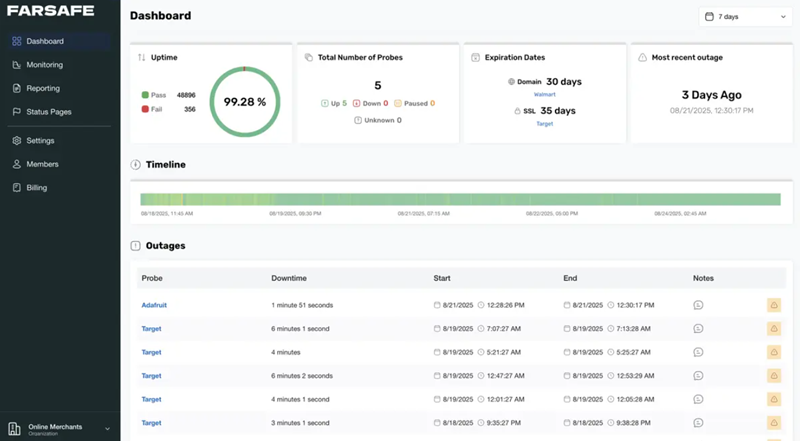
Telemetry and observability
Streaming telemetry, syslog aggregation, and metric collection provide the observability needed for automated remediation and analytics. Telemetry pipelines send structured data to collectors and time-series databases where alerting rules or machine learning models detect anomalies and trigger automated playbooks.
Orchestration and intent
Orchestration layers translate high-level business intent into device-level configurations. Intent-based networking systems and Software-Defined Networking (SDN) controllers centralize policy enforcement and path computation, helping to ensure consistent policy application across hybrid environments.
Benefits for operations and engineering
Adopting network automation tools yields measurable operational benefits:
- Speed: Faster provisioning and change rollouts reduce lead time for new services.
- Consistency: Versioned configurations and templates lower the risk of misconfiguration.
- Scalability: Automated workflows scale across sites and cloud regions with less manual effort.
- Visibility: Centralized logging and telemetry improve troubleshooting and capacity planning.
Implementation approaches and patterns
Incremental automation
Begin with small, well-scoped tasks such as automated backups, bulk configuration changes, or standardized onboarding. Incremental delivery reduces risk and allows teams to validate tooling, testing, and rollback procedures before wider rollout.
Template-driven configuration and version control
Store device templates and playbooks in version control to enable change tracking, peer review, and traceability. Combine templates with parameter stores to support multi-tenant or multi-site deployments while preserving uniformity.
Integration with CI/CD and ITSM
Integrate automation pipelines with CI/CD systems and IT service management (ITSM) platforms to control workflow approvals, change windows, and audit trails. This integration supports coordinated deployments across network, compute, and application stacks.
Security, governance, and compliance
Automation introduces both benefits and risks for security and compliance. Centralized management allows consistent application of security policies, but programmatic access increases the attack surface if credentials or APIs are not properly secured.
- Credential management: Use vaulted secrets and role-based access controls to limit who or what can execute automated workflows.
- Audit and logging: Maintain immutable logs of automation actions for forensic analysis and compliance reporting.
- Testing: Validate changes in staging environments and use canary rollouts or dry-run modes before production application.
Common challenges and how to address them
Adoption can be slowed by device heterogeneity, legacy platforms with limited API support, and organizational silos between network and software teams. Common mitigation strategies are: mapping inventory and capabilities, using adapters or intermediate controllers where direct APIs are missing, and establishing cross-functional teams for design and runbooks.
Measuring success
Track metrics such as mean time to provision, number of manual changes vs automated, frequency of configuration errors, and time to detect and remediate incidents. These metrics help build a business case and guide further automation investments.
Future trends
Trends include greater use of intent-based networking, expanded telemetry for real-time assurance, tighter integration between network and application CI/CD pipelines, and more widespread use of model-driven APIs across vendors. Research in networking and standards bodies such as the IETF and publications by academic and standards organizations (for example, IEEE and NIST reports) inform these trends and recommended practices.
Getting started checklist
- Inventory devices and classify by API capability and OS versions.
- Identify high-value automation candidates (repetitive, high-risk tasks).
- Introduce version-controlled templates and staged testing environments.
- Enforce least-privilege access, auditing, and secret management.
- Measure outcomes and iterate on tooling and governance.
Resources and standards bodies to consult
Standards bodies such as the IETF publish protocols and data models relevant to automation, while organizations like NIST provide guidance on cybersecurity controls that apply to automated systems. Academic literature and industry white papers offer research findings on telemetry, intent engines, and orchestration patterns.
FAQ: What are network automation tools?
Network automation tools are software systems and frameworks that automate configuration, provisioning, monitoring, and remediation tasks across network devices and services. They rely on APIs, model-driven data (for example, YANG), telemetry streams, and orchestration layers to implement repeatable workflows and policies.
How do network automation tools improve reliability?
Automation enforces consistent configurations, reduces manual entry errors, and enables rapid rollback or remediation. Coupled with observability and testing, automation can shorten detection and repair cycles, improving overall network reliability.
Which standards and organizations are relevant to network automation?
Key organizations include the Internet Engineering Task Force (IETF) for protocols and data models, the National Institute of Standards and Technology (NIST) for cybersecurity guidance, and IEEE for networking research and standards. Consulting specifications and best practices from these bodies helps align automation efforts with established standards.
What are common pitfalls when deploying automation?
Common pitfalls include insufficient testing, lack of governance or credential control, attempting broad automation too quickly, and neglecting observability. Starting small, using version control, and integrating automated tests and audits reduces these risks.