Red Hat OpenShift Guide: Mastering Cloud-Native Development and Deployment
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Introduction
Red Hat OpenShift is a Kubernetes-based container platform designed to help teams build, deploy, and manage cloud-native applications at scale. This guide explains core concepts, architecture, deployment models, security considerations, and practical best practices for organizations evaluating or operating OpenShift clusters.
- OpenShift packages Kubernetes with developer and operational tooling for production use.
- Key components include the OpenShift API, container runtime, Operators, and an integrated registry.
- Supports on-premises, public cloud, and hybrid deployments with templates for CI/CD and security policies.
- Adopting platform best practices improves reliability, observability, and compliance posture.
Red Hat OpenShift Overview and Benefits
At its core, Red Hat OpenShift extends upstream Kubernetes with enterprise capabilities such as integrated developer tools, automated operations, policy-driven security, and multi-cluster management. Organizations choose OpenShift for accelerated application delivery, standardized runtimes, and features that simplify continuous integration and continuous deployment (CI/CD).
Benefits for development and operations
OpenShift streamlines developer workflows with features like source-to-image (S2I) builds, developer consoles, and built-in CI/CD pipelines. For operators, it offers automated upgrades, health checks, and lifecycle management that reduce the operational burden of maintaining Kubernetes infrastructure.
Key Components and Architecture
Kubernetes control plane and nodes
OpenShift uses a Kubernetes control plane (API server, controller manager, etcd) and worker nodes running container workloads. The platform configures network overlays, service discovery, and storage integrations to enable stateful and stateless applications.
Container runtime and image registry
Container runtimes execute application images; OpenShift supports OCI-compatible images and includes an integrated image registry for storing container artifacts and image streams used by build processes and deployments.
Operators and automation
Operators encapsulate operational knowledge to automate management tasks for complex services. Using the Operator Framework and Operator Lifecycle Manager (OLM), OpenShift simplifies installing, upgrading, and configuring platform components and third-party services.
Deployment Models and Infrastructure Options
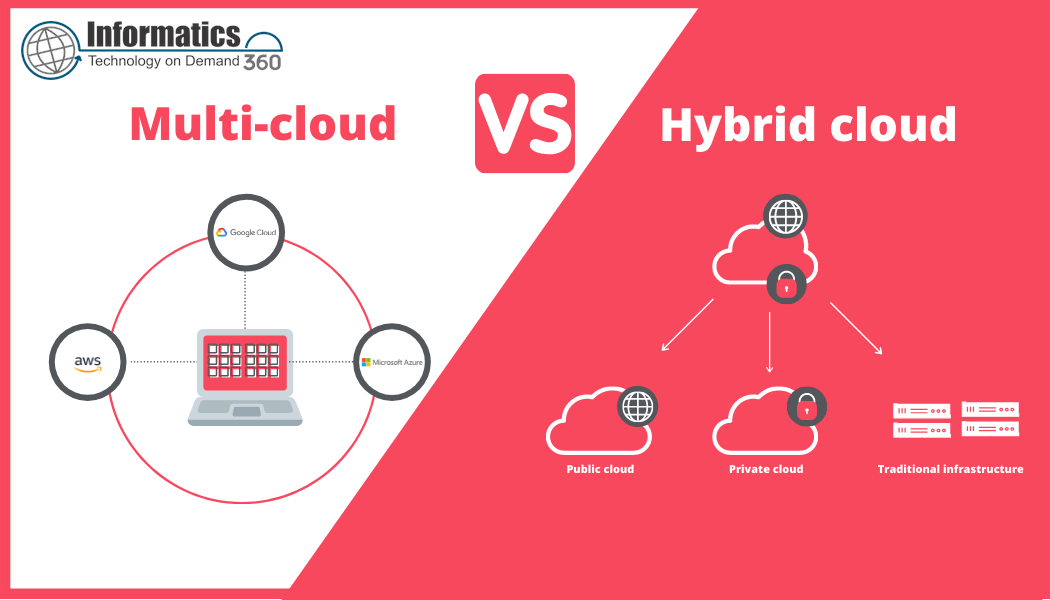
On-premises, public cloud, and hybrid
OpenShift supports multiple infrastructure footprints: bare metal or virtualized on-premises deployments, hosted clusters on major clouds, and hybrid models that combine on-prem and cloud resources. Multi-cluster management tools facilitate policy enforcement and application distribution across environments.
Managed and self-managed options
Options range from fully managed control planes to self-managed clusters where organizations maintain nodes and upgrades. Selection depends on operational maturity, compliance requirements, and resource constraints.
Security, Compliance, and Governance
Identity, access control, and policy
OpenShift integrates with enterprise identity providers and offers role-based access control (RBAC), network policies, and pod security standards to enforce least privilege. Combining platform policies with runtime monitoring improves security posture.
Compliance and auditing
Audit logs, configuration management, and standardized control plane configurations help support compliance frameworks. Reference guidance from regulators and standards bodies such as NIST for mapping platform controls to compliance requirements.
Operational Best Practices
Cluster provisioning and lifecycle
Automate cluster provisioning using infrastructure-as-code tools and follow a documented lifecycle for upgrades and backups. Regularly test disaster recovery procedures and validate backup restoration of etcd and application data.
Observability and troubleshooting
Implement centralized logging, metrics, and tracing to detect issues early. Use health probes, circuit breakers, and rate limiting to increase resilience. Leverage platform-provided dashboards and Prometheus exporters for monitoring cluster and application health.
Getting Started and Migration Considerations
Proof of concept and pilot projects
Begin with a small pilot focusing on a single application or team to validate processes, CI/CD pipelines, and security baselines. Measure deployment frequency, mean time to recovery (MTTR), and resource utilization to refine patterns before broader rollout.
Application modernization and refactoring
Assess applications for container readiness. Prioritize stateless services and gradually refactor or replatform stateful components. Use standardized build and deployment templates to reduce configuration drift across teams.
Integrations and Ecosystem
CI/CD, service mesh, and storage
OpenShift integrates with common CI/CD systems, service meshes, and persistent storage providers. Service meshes can enable traffic management and observability, while container-native storage plugins provide persistent volumes for stateful workloads.
Community and standards
OpenShift aligns with cloud-native standards such as Kubernetes and the Cloud Native Computing Foundation (CNCF) projects. Academic and industry research published in venues like IEEE and ACM can provide methodologies for benchmarking and platform evaluation.
For official product documentation and platform details, consult the vendor's documentation: Red Hat OpenShift documentation.
Conclusion
Red Hat OpenShift offers a production-ready Kubernetes distribution with enterprise features for developers and operators. By combining standardized runtimes, automation via Operators, and integrated developer tooling, organizations can accelerate cloud-native application delivery while maintaining control over security and governance.
FAQ
What is Red Hat OpenShift?
Red Hat OpenShift is an enterprise Kubernetes platform that bundles Kubernetes with developer tools, CI/CD integration, Operators, and management capabilities to facilitate the deployment and operation of cloud-native applications.
How does OpenShift differ from upstream Kubernetes?
OpenShift adds enterprise features to upstream Kubernetes, including integrated developer consoles, image registries, curated operator catalogs, automated lifecycle management, security defaults, and vendor support for production environments.
What are common use cases for adopting OpenShift?
Common use cases include modernizing legacy applications, building microservices architectures, standardizing deployment pipelines across teams, and supporting multi-cloud or hybrid cloud strategies requiring consistent tooling and governance.
What security controls should be configured first on a new OpenShift cluster?
Prioritize identity integration, RBAC policies, network segmentation via network policies, audit logging, and secure image scanning as initial controls to reduce the attack surface and maintain visibility into cluster activity.