How a Virginia Tech Professor Uses Computer Games to Advance AI and Cybersecurity
Get a free topical map and start building content authority today.
An interdisciplinary research approach now often uses interactive environments to train and test artificial intelligence systems. A Virginia Tech professor is leveraging computer games and simulated environments to study machine learning, adversarial strategies, and cyber defense, producing reproducible results for both academic research and practical cybersecurity evaluation.
- Computer games provide controllable, repeatable environments for training AI and testing cyber defenses.
- Techniques include reinforcement learning, multi-agent simulation, and adversarial training.
- Research is supported by university labs, federal grants, and partnerships with standards bodies.
- Ethical, reproducibility, and evaluation challenges remain; standards from organizations such as NIST and IEEE inform best practices.
Virginia Tech professor advances AI and cybersecurity using computer games
Researchers at universities including Virginia Tech use game engines and purpose-built simulators to accelerate work in reinforcement learning, anomaly detection, and automated defense. These controlled settings mimic real-world complexity while allowing safe experimentation with adversarial techniques and automated attackers.
Why computer games are useful for AI and cybersecurity research
Controlled, repeatable experiments
Games and simulations allow precise control over environment variables—network topology, user behavior, traffic patterns, and threat models—making it possible to reproduce experiments and benchmark algorithms. This is important for publishing results and for peer validation through academic conferences and journals managed by organizations such as ACM and IEEE.
Rich, scalable scenarios
Modern game engines and multi-agent platforms can model complex interactions at scale, from virtual economies to coordinated cyber attacks. Synthetic data generated in these environments helps train machine learning models where labeled real-world data is scarce or sensitive.
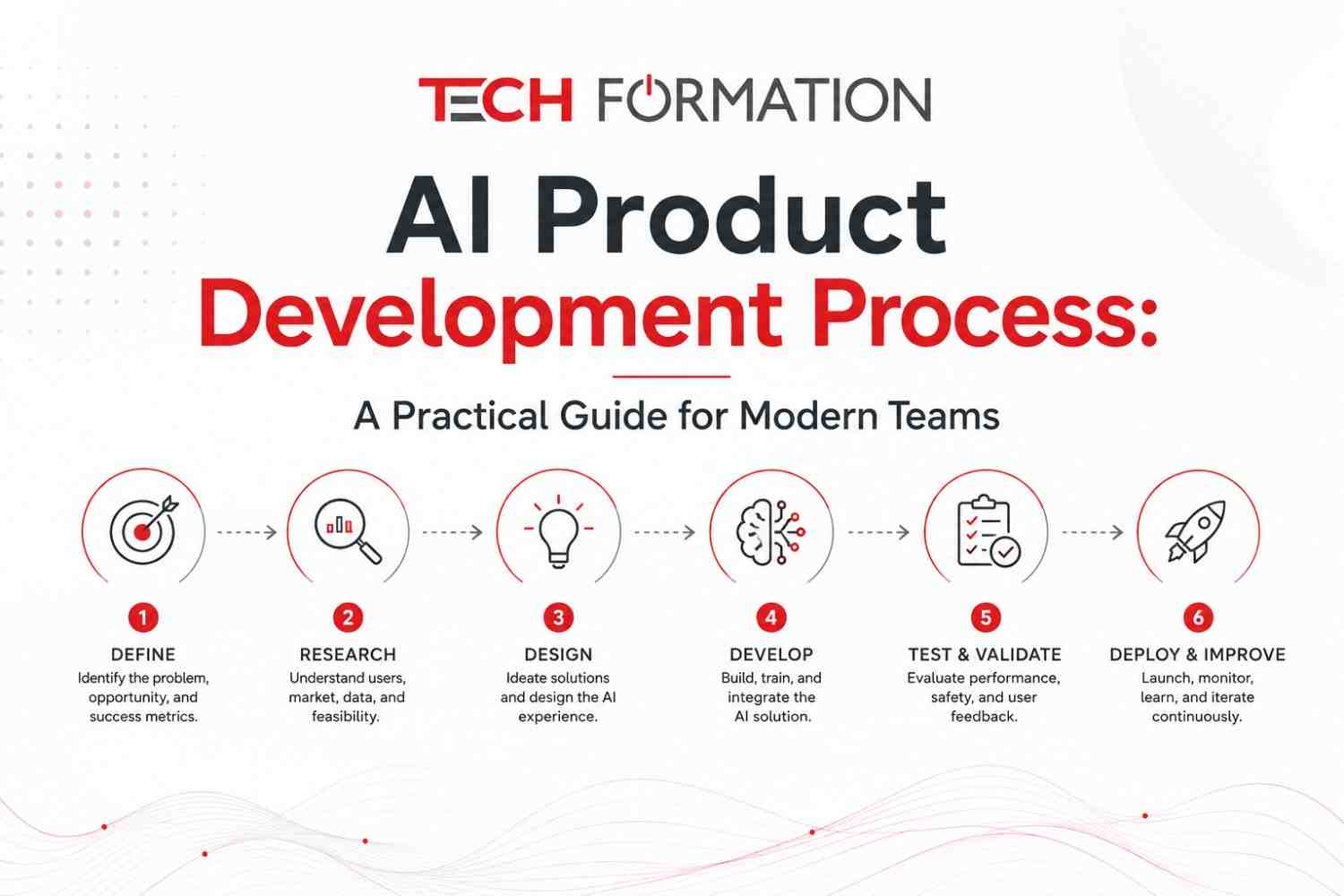
Research methods and technical approaches
Reinforcement learning and game-theoretic models
Reinforcement learning (RL) algorithms learn policies through trial and error in simulated tasks. In cybersecurity research, RL can model both attackers and defenders, producing strategies that adapt to evolving tactics. Game-theoretic approaches formalize strategic interactions, helping to identify equilibrium behaviors under different assumptions.
Adversarial training and red-team simulations
Adversarial methods create realistic threat scenarios: red-team agents probe vulnerabilities while blue-team agents learn detection and mitigation. These simulated engagements enable automated stress testing of intrusion detection systems and evaluate resilience under coordinated attacks.
Synthetic data and transfer learning
AI models trained on synthetic traces from simulations can be fine-tuned on smaller real-world datasets, a practice known as transfer learning. This reduces reliance on sensitive operational data while retaining performance improvements for tasks such as anomaly detection and behavior profiling.
Applications in cybersecurity and AI
Improving intrusion detection and response
Simulations permit evaluation of detection algorithms against novel attack patterns, enabling the development of faster response strategies and automated playbooks. Cyber ranges—interactive, sandboxed environments—are commonly used in education and professional training.
Evaluating robustness and explainability
Game-like scenarios help assess model robustness to adversarial inputs and environmental shifts. Explainability tools applied in these settings can make automated decisions more transparent for operators and auditors.
Partnerships, funding, and standards
Work in this area is often supported by federal agencies, university research centers, and industry partnerships. Funders and standards bodies such as the National Science Foundation (NSF), the National Institute of Standards and Technology (NIST), and professional groups like IEEE provide frameworks for reproducibility, responsible AI, and cybersecurity best practices. For more information about institutional efforts at Virginia Tech, see the university's research pages: Virginia Tech.
Limitations and ethical considerations
Transferability to real-world systems
Simulated environments cannot perfectly reproduce all aspects of operational networks and human behavior. Careful validation against real-world data and conservative deployment practices are necessary to avoid overestimating system performance.
Ethics, dual use, and responsible disclosure
Research that models offensive capability has dual-use potential. Ethical review, adherence to disclosure policies, and alignment with community standards—such as those published by ACM, IEEE, and relevant institutional review boards—help manage risks.
Outlook and ongoing challenges
Integrating game-based simulation with hardware-in-the-loop testing, federated learning, and live operational feedback loops remains an active research area. Continued collaboration among academic researchers, standards organizations, and practitioners will shape how techniques developed in simulated games are validated and adopted in production cybersecurity systems.
References and authoritative sources
Relevant organizations that publish guidance or fund related work include the National Science Foundation (NSF), the National Institute of Standards and Technology (NIST), ACM, and IEEE. These bodies provide resources on reproducibility, cybersecurity frameworks, and AI ethics that inform research and deployment decisions.
How does a Virginia Tech professor use computer games to improve AI and cybersecurity?
Computer games and simulated environments serve as laboratories where AI agents are trained and evaluated under repeatable, controlled conditions. Methods such as reinforcement learning, adversarial training, and multi-agent simulation are applied to test defensive algorithms, discover vulnerabilities, and develop robust, adaptive systems.
What are the main research techniques mentioned?
Main techniques include reinforcement learning, adversarial training, game-theoretic modeling, synthetic data generation, transfer learning, and multi-agent systems.
Are results from simulated environments reliable for real-world deployment?
Simulations provide valuable insights but require careful validation against real operational data. Best practices involve staged deployment, continuous monitoring, and alignment with standards from organizations such as NIST and NSF.
What ethical safeguards are recommended?
Recommended safeguards include institutional review, responsible disclosure policies, compliance with professional codes of conduct, and collaboration with standards bodies to mitigate dual-use risks and ensure transparent, accountable research.