Selecting a Reliable SaaS Application Development Company: Practical Criteria and Checklist
Get a free topical map and start building content authority today.
Choosing the right SaaS application development company is a critical step for organizations planning cloud-based software. A reliable SaaS application development company balances secure architecture, compliant operations, predictable commercial terms, and proven delivery practices to reduce risk and speed time to value.
- Prioritize security, compliance, and multitenant architecture.
- Verify development processes: CI/CD, testing, observability.
- Check SLAs, support, pricing model, and exit strategies.
- Validate vendors with references, case studies, and trial engagements.
- Look for independent certifications and alignment with standards.
How to evaluate a SaaS application development company
Technical expertise and architecture
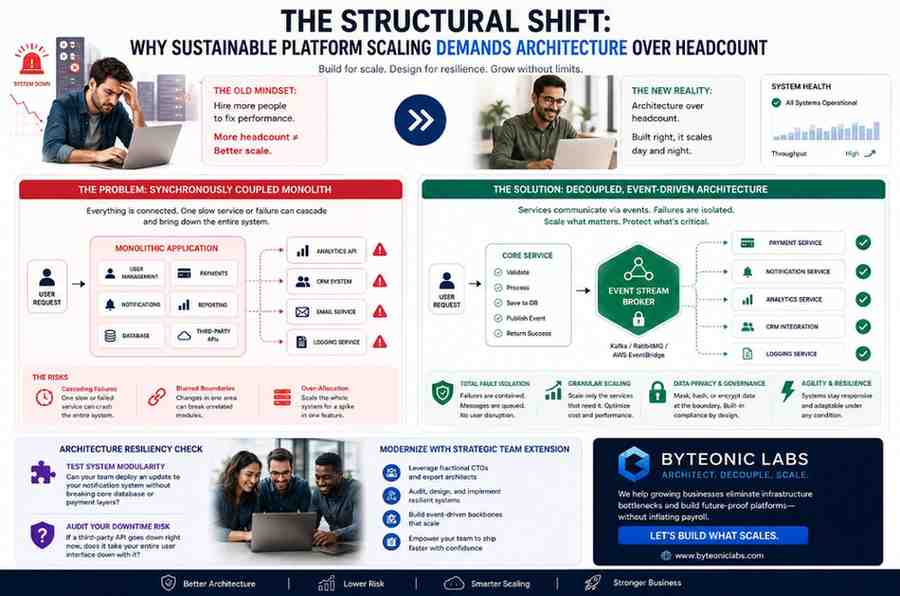
Assess experience with cloud-native design patterns such as microservices, containerization, orchestration, multitenancy, and API-first development. Confirm the company can design for scalability, high availability, and cost-effective resource use. Ask about data partitioning strategies, schema evolution, tenant isolation, and support for data portability and interoperability.
Platform and integration capabilities
Ensure the team has experience integrating with identity providers, third-party APIs, event streaming, and common enterprise systems. Check their approach to API design (versioning, rate limiting, authentication) and whether they provide clear developer documentation and SDKs to support partner integrations.
Security, compliance, and data protection
Controls, certifications, and regulatory alignment
Security is a top selection criterion. Ask about threat modeling, secure SDLC practices, encryption in transit and at rest, key management, and incident response. Look for compliance and assurance reports such as ISO/IEC 27001, SOC 2, and familiarity with data protection laws like the EU General Data Protection Regulation (GDPR). For guidance on security frameworks and best practices, review materials from official standards bodies such as NIST.
Penetration testing and vulnerability management
Confirm regular third-party penetration testing and an active vulnerability management program. Review the vendor’s policies for patching, disclosure, and timelines for remediation. Ask whether security findings are shared under NDA or included in contractual obligations.
Development process, testing, and operations
DevOps, CI/CD, and quality assurance
Reliable vendors use automated CI/CD pipelines, infrastructure-as-code, automated testing (unit, integration, and regression), and can demonstrate a history of frequent, safe releases. Request details about their branching strategy, code review practices, and automated test coverage metrics.
Monitoring, observability, and SRE practices
Operational maturity includes logging, metrics, distributed tracing, alerting thresholds, and runbooks. Ask how incidents are handled, mean time to detect (MTTD), and mean time to recover (MTTR). Clarify roles for ongoing operations—whether the vendor provides managed operations, a shared responsibilities model, or hands-off handover.
Commercial terms, SLAs, and support
Pricing models and total cost of ownership
Compare fixed-price, time-and-materials, and outcome-based contracts. Evaluate cost drivers such as active user growth, data storage, and API usage. Consider total cost of ownership including onboarding, customization, training, and ongoing operational fees.
Service-level agreements and exit strategy
Review SLAs for uptime, performance, support response times, and remedies for breaches. Include contractual terms addressing data ownership, data export formats, assistance with migration, and intellectual property rights. A clear exit plan reduces vendor lock-in risk.
Selecting and validating candidate companies
References, case studies, and proof of work
Request case studies relevant to industry, scale, and technical challenges. Speak with references about delivery timelines, communication, and post-launch support. Where possible, review code samples, architecture diagrams, or open-source contributions to verify technical claims.
Pilot projects and phased engagements
Start with a small pilot or a time-limited sprint to validate capabilities, team fit, and delivery cadence. Use measurable success criteria for pilots (performance, feature completeness, integration ease) before committing to larger scopes.
Contracting and governance
Establish governance rhythms: checkpoints, steering committees, and change control processes. Include acceptance criteria, security obligations, and escalation paths in the contract. Use clear KPIs and reporting templates to track progress.
Post-selection checklist
- Verify corporate stability and insurance coverage.
- Confirm developer access controls and segregation of duties.
- Agree on backup policies and disaster recovery plans.
- Document SLAs, maintenance windows, and on-call rotations.
Final considerations
Choosing a reliable partner requires balancing technical fit, security posture, operational maturity, commercial clarity, and cultural alignment. Time invested in due diligence—architecture reviews, security assessments, pilot work—reduces downstream risk and improves long-term outcomes.
Frequently asked questions
What should be included in an SLA when hiring a SaaS application development company?
An SLA should define uptime/availability targets, performance metrics, support response and resolution times, maintenance windows, penalties or credits for breaches, security obligations, and data handling commitments including exportability and deletion procedures.
How can a buyer verify security practices without exposing sensitive information?
Request redacted audit reports (SOC 2, ISO 27001 certificates), summary penetration test reports, a security whitepaper, and a completed security questionnaire. Use NDAs and technical scopes that allow verification while protecting sensitive details.
When is a pilot project recommended before a full engagement with a SaaS application development company?
Pilots are recommended when adopting new technology, integrating complex systems, validating multitenant behavior, or assessing team fit. A pilot helps demonstrate delivery capability and surface architectural or operations risks early.
How to choose a SaaS application development company if regulatory compliance is a requirement?
Prioritize vendors with relevant certifications (e.g., ISO/IEC 27001, SOC 2) and documented experience in the required regulatory environment. Confirm data residency, processing agreements, and contractual commitments to comply with applicable rules such as GDPR or industry-specific standards.