How to Control BYOD Devices in Enterprises Without Compromising Security
Get a free topical map and start building content authority today.
Bring Your Own Device policies are common in modern workplaces. Employees prefer using their own laptops, smartphones, and tablets for work. It increases flexibility and sometimes reduces hardware costs.
However, controlling BYOD devices in enterprises is one of the biggest challenges for IT security teams.
When personal devices access company data, the risk of data leaks, compliance violations, and cyber attacks increases. Without a structured strategy, BYOD can quickly become a security liability.
This guide explains how enterprises can control BYOD devices securely while maintaining productivity and user privacy.
Why BYOD Is a Security Challenge for Enterprises
Before discussing solutions, it is important to understand the risks.
BYOD environments introduce:
-
Limited visibility into personal devices
-
Mixing of personal and corporate data
-
Inconsistent security configurations
-
Delayed patch updates
-
Higher risk of lost or stolen devices
Unlike company-owned devices, personal devices are not always configured according to corporate IT standards. Employees may disable security settings, delay updates, or install risky applications.
From a cybersecurity perspective, unmanaged BYOD endpoints expand the attack surface.
Step 1: Establish a Clear BYOD Security Policy
The first step in controlling BYOD devices is documentation.
A well-defined BYOD policy should clearly outline:
-
Which devices are allowed
-
Minimum operating system requirements
-
Mandatory security settings
-
Data access rules
-
Monitoring and privacy boundaries
-
Consequences of non-compliance
Employees must understand that access to corporate systems requires meeting security standards.
Clear communication prevents future conflicts and builds trust.
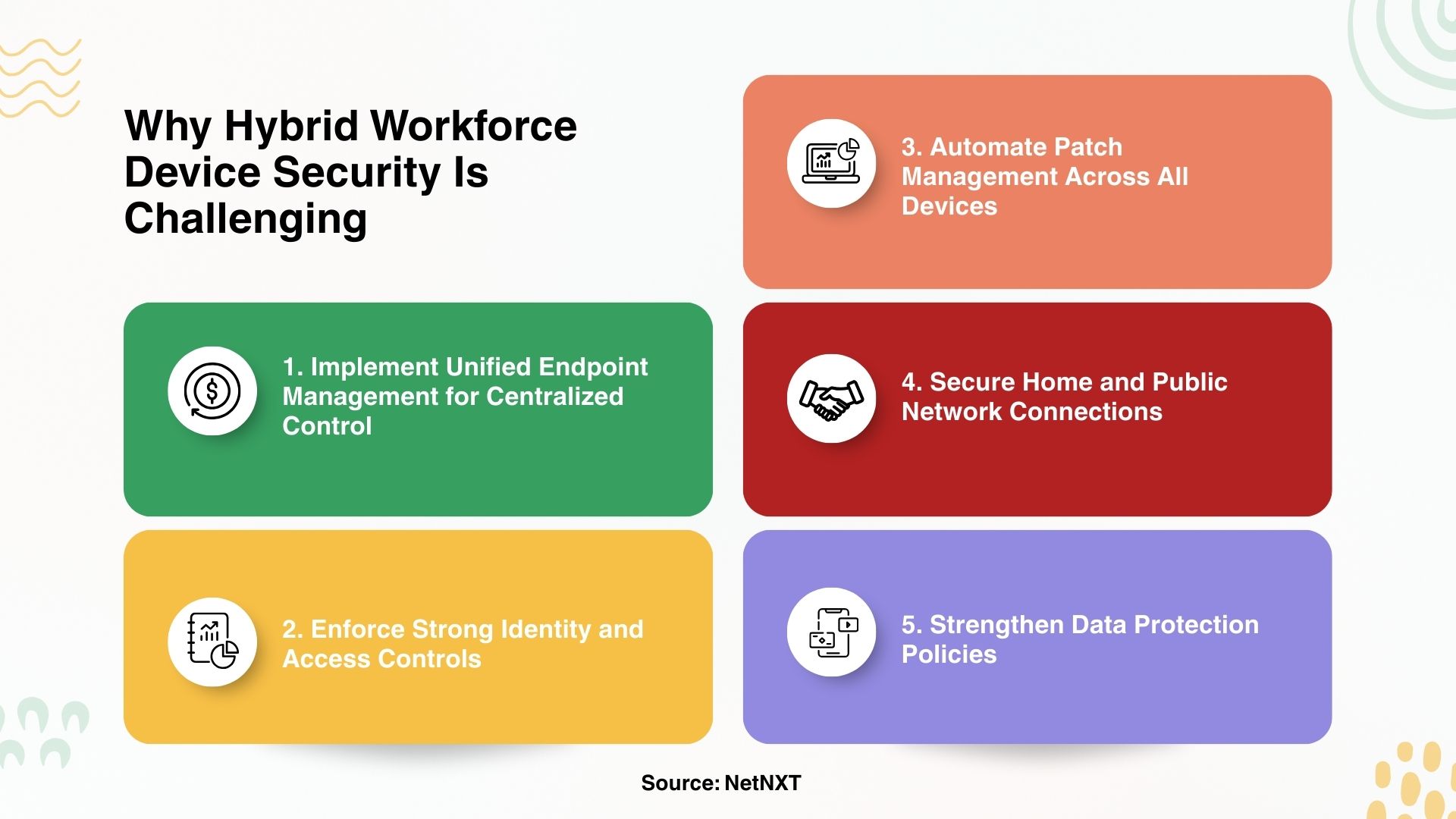
Step 2: Use Unified Endpoint Management for BYOD Control
Manual monitoring is not scalable. Enterprises need centralized control.
A Unified Endpoint Management solution allows IT teams to:
-
Enroll personal devices securely
-
Enforce encryption requirements
-
Apply security configurations
-
Monitor compliance status
-
Remotely remove corporate data if needed
This ensures that personal devices meet enterprise IT security standards before accessing business resources.
If you want to understand the foundation of this approach, refer to our previous guide on Unified Endpoint Management and why centralized device visibility is critical in modern enterprises.
Organizations often combine UEM with managed IT services to maintain consistent policy enforcement. NetNXT, for example, supports enterprises by integrating Unified Endpoint Management with broader cybersecurity and network security strategies. This helps businesses secure BYOD environments without increasing operational burden.
Step 3: Separate Corporate and Personal Data
One of the biggest concerns with BYOD is privacy.
Employees worry that IT teams may access personal photos, messages, or apps. Enterprises worry about sensitive company data being exposed.
The solution is data separation.
Modern device management platforms enable:
-
Containerization of corporate applications
-
Separate encrypted storage for business data
-
Controlled file sharing
-
Selective wipe of corporate data only
If an employee leaves the company, IT can remove business information without affecting personal content.
This balance protects both enterprise data and employee privacy.
Step 4: Enforce Identity-Based Access Control
Controlling BYOD devices requires more than device configuration. Identity must also be verified.
Enterprises should implement:
-
Multi-factor authentication
-
Role-based access control
-
Conditional access based on device compliance
-
Continuous identity verification
Platforms such as JumpCloud integrate identity and device posture checks. This ensures that only authorized users on compliant devices can access sensitive systems.
If a device falls out of compliance, access can be restricted automatically.
Step 5: Automate Patch and Security Updates
Unpatched personal devices are a major risk.
Enterprises must require:
-
Automatic operating system updates
-
Updated antivirus or endpoint protection software
-
Removal of vulnerable applications
Unified Endpoint Management platforms can enforce minimum patch levels before granting access.
This significantly reduces exposure to ransomware and malware attacks.
Step 6: Monitor and Audit BYOD Devices Regularly
Security is not static.
IT teams should continuously monitor:
-
Device encryption status
-
Patch compliance
-
Application risk levels
-
Access logs
Regular audits ensure ongoing compliance with regulations such as GDPR, HIPAA, or SOC 2.
Enterprises that lack internal bandwidth often rely on managed security services to maintain continuous monitoring and reporting. This approach strengthens cybersecurity while keeping IT operations manageable.
Step 7: Limit Access Based on Risk Level
Not all employees require full access to all systems.
To reduce risk:
-
Provide least-privilege access
-
Restrict administrative rights
-
Block access from high-risk devices
-
Apply stronger controls to sensitive departments
By limiting access based on role and risk, enterprises reduce the impact of potential device compromise.
Common BYOD Mistakes Enterprises Should Avoid
Many organizations weaken their security posture by:
-
Allowing unmanaged devices to connect freely
-
Ignoring patch compliance checks
-
Overlooking identity integration
-
Failing to define clear privacy boundaries
-
Not having a device de-enrollment process
Avoiding these mistakes requires a structured framework that connects device management, IT security policies, and identity control.
Final Thoughts
BYOD policies are here to stay. They support flexibility, employee satisfaction, and operational efficiency. But without strong controls, they can expose enterprises to serious cybersecurity risks.
Controlling BYOD devices in enterprises requires:
-
Clear policies
-
Unified Endpoint Management
-
Identity-driven access control
-
Automated patching
-
Data separation
-
Continuous monitoring
Businesses that treat BYOD as part of their broader IT services and cybersecurity strategy build stronger protection without sacrificing flexibility.
If your organization is evaluating how to implement secure BYOD management, exploring a structured Unified Endpoint Management approach through NetNXT can help align device control with long-term security and compliance goals.
Frequently Asked Questions
1. What is BYOD in enterprises?
BYOD stands for Bring Your Own Device. It allows employees to use personal devices such as laptops and smartphones for work purposes under company policies.
2. How can enterprises secure personal devices used for work?
Enterprises can secure BYOD devices using Unified Endpoint Management, enforcing encryption, applying access controls, and separating corporate data from personal data.
3. Is BYOD safe for regulated industries?
Yes, but only if strict compliance policies, encryption standards, identity verification, and monitoring systems are enforced consistently.
4. Can IT access personal data on BYOD devices?
With modern containerization and data separation tools, IT teams can manage corporate data without accessing personal content, protecting employee privacy.