Top DevOps Tools for IT Operations in the USA: A Practical Selection Guide
Get a free topical map and start building content authority today.
Choosing the right DevOps tools for IT operations can reduce downtime, speed deployments, and lower operational overhead across cloud and on-premises environments. This guide maps tool categories, trade-offs, and a practical checklist to streamline operations in the USA tech context.
Intent: Commercial Investigation
This article lists the key DevOps tool categories—version control, CI/CD, infrastructure-as-code, configuration management, container orchestration, observability, security, and collaboration—explains trade-offs, provides a CALMS-based checklist, a short real-world scenario, practical tips, and common mistakes to avoid.
DevOps tools for IT operations: categories and what each solves
A practical inventory organizes tools by the operational problem they solve. Use the categories below as a selection map when assembling a toolchain for teams that need consistent deployments, fast recovery, and measurable change control.
Version control and source control management
Centralized source control is the system of record for code, infra-as-code, and configuration. Look for branch workflows, access controls, audit logging, and integrations with CI/CD pipelines.
Continuous integration and continuous delivery (CI/CD)
CI/CD automates build, test, and deployment stages. When evaluating CI/CD tools, compare pipeline-as-code support, parallelism, artifact management, and security gating for production releases. These are core to any DevOps automation tools list for a mature team.
Infrastructure as Code (IaC) and configuration management
IaC tools codify environment provisioning and drift detection. Configuration management handles state and desired configuration on running systems. Prioritize idempotence, state management, and multi-cloud capability.
Containerization and orchestration
Containers package services; orchestration schedules, scales, and heals them. Evaluate scheduling intelligence, multi-cluster support, and service discovery features for production-grade operations.
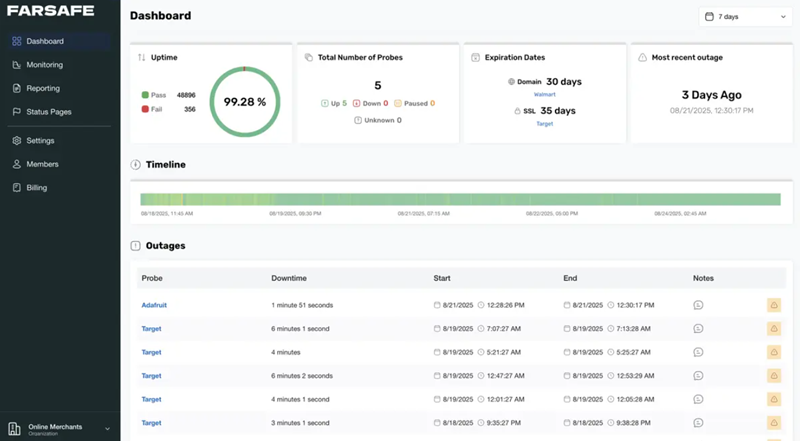
Observability: monitoring, logging, tracing
Observability solutions collect metrics, logs, and traces to enable fast incident diagnosis and SLO-driven operations. Consider retention policies, query performance, and alerting fidelity.
Security and compliance tooling
Security tools in the DevOps pipeline can include static analysis, dependency scanning, secret management, and runtime protection. Integrate security checks early in pipelines to reduce vulnerabilities shipped to production.
Collaboration, incident response, and runbooks
Reliable incident workflows, runbooks, and post-incident analysis tools close the loop on operational learning. Look for integration with ticketing, chat, and alerting channels.
How to pick: prioritized checklist (CALMS framework + checklist)
Apply the CALMS framework—Culture, Automation, Lean, Measurement, Sharing—combined with a short checklist to score candidate tools.
- Culture: Does the tool support cross-team collaboration and shared ownership?
- Automation: Does it enable reliable automation and reduce manual steps?
- Lean: Does the tool let teams iterate quickly with limited waste?
- Measurement: Does it expose meaningful metrics and SLO support?
- Sharing: Are reports, dashboards, and runbooks easily shareable?
Deployment Readiness Checklist:
- Pipeline-as-code configured and tested in staging.
- IaC in version control with reviewed state handling.
- Monitoring and alerting on critical paths and SLOs.
- Access controls and secrets management enforced.
- Automated rollback, canary, or blue/green deployment configured.
Core tool categories with representative examples and trade-offs
This section provides representative tools by category; descriptions focus on trade-offs and selection criteria rather than endorsements.
CI/CD and automation engines
Choose builders that scale with parallel runs and pipeline-as-code. Trade-offs include managed services (less maintenance, more vendor lock-in) versus self-hosted runners (more control, more ops work).
Infrastructure and configuration
Declarative IaC tools make environments reproducible but impose state-management patterns. Imperative scripting is flexible but harder to audit. Evaluate teams' skillsets before locking in a model.
Containers and orchestration
Kubernetes-style orchestration standardizes deployments across clusters but has a steeper operational cost than simpler container services. For smaller teams, managed orchestration reduces maintenance burden.
Observability and SRE tooling
Full observability stacks require investment in instrumentation and alert tuning. Lightweight monitoring is faster to start but may miss systemic issues. Plan for metrics, tracing, and log correlation from day one.
Short real-world scenario
Example: A mid-sized retail company needed to deploy new services twice weekly without downtime. The operations team adopted a pipeline-as-code CI/CD system with IaC-managed staging environments, container orchestration for scaling, and an observability stack keyed to SLOs. After three months, deployment time dropped 70% and mean time to recovery (MTTR) improved by 60% because automated tests and rollbacks reduced manual remediation.
Practical tips to implement a DevOps toolchain
- Start with one high-impact workflow (e.g., CI for the payment service) and standardize that pipeline before expanding.
- Automate small, repeatable tasks first—build, test, and deploy are better automated early than later.
- Instrument applications and platform components for metrics and traces before a major release to support observability-driven operations.
- Use feature flags and progressive rollouts to reduce blast radius during releases.
Common mistakes and trade-offs to watch
Common mistakes
- Assembling many point solutions without integration planning—creates silos and tooling sprawl.
- Underinvesting in monitoring and alert tuning—leads to noisy alerts and ignored signals.
- Choosing tools for feature lists instead of team operational capacity—overly complex tools can slow teams down.
Trade-offs
Managed vs self-hosted: managed services reduce ops but can increase costs and lock-in. Standardization vs flexibility: standard stacks simplify onboarding but may force compromises for edge use cases.
Core cluster questions (for internal linking and related content)
- Which DevOps tool categories are essential for on-call reliability?
- How to evaluate CI/CD tools for enterprise-scale pipelines?
- What is the role of Infrastructure as Code in multi-cloud operations?
- How to measure success after deploying a new DevOps toolchain?
- Which observability patterns reduce mean time to recovery (MTTR)?
Standards and best practices reference
Follow recognized standards and guidance for secure software supply chains and operational resilience; this helps align tool choice and policies with industry expectations. See guidance from the National Institute of Standards and Technology for frameworks and best practices: NIST.
FAQ
What are the essential DevOps tools for IT operations?
Essential tools cover source control, CI/CD, IaC/configuration management, container orchestration, observability (metrics/logs/tracing), security scanning, and incident management. The specific products depend on team size, compliance needs, and cloud footprint.
How should teams evaluate DevOps automation tools?
Score tools on automation capability, integration support, scalability, observability, security features, and total cost of ownership. Use a small proof-of-concept that exercises critical paths before full adoption.
Can a small IT team adopt the same tools as a large enterprise?
Yes, but scale and operational capacity matter. Smaller teams benefit from managed services and simplified orchestration models, while larger enterprises often require self-hosted and highly configurable solutions.
How does observability fit into the DevOps toolchain?
Observability provides the feedback loop for SRE and DevOps practices—metrics for SLIs/SLOs, logs for forensic analysis, and tracing for request flow. Instrumentation should be integrated into CI/CD and release processes.
What are the first steps to reduce deployment risk with new tools?
Begin with a single critical service, implement pipeline-as-code with automated testing, add feature flags for controlled rollouts, and ensure monitoring with alerting on SLO breaches before broad rollout.