Practical GitHub Actions CI/CD Setup: Step-by-Step Guide and Checklist

Get a free topical map and start building content authority today.
This guide explains a practical GitHub Actions CI/CD setup that builds, tests, and deploys code automatically. The examples and checklist focus on repeatable steps for real projects: create a workflow, use runners and matrix builds, secure secrets, and push releases. The phrase "GitHub Actions CI/CD setup" appears throughout as the central objective.
Follow a clear BUILD-TEST-DEPLOY checklist to create a GitHub Actions CI/CD setup: add a YAML workflow, run builds and tests using matrix jobs, publish artifacts, and automate deployments with environment protection. Includes a Node.js example, practical tips, and common mistakes to avoid.
GitHub Actions CI/CD setup: quick overview
GitHub Actions uses YAML workflows stored in .github/workflows to define automated CI/CD pipelines. Workflows contain jobs that run on GitHub-hosted or self-hosted runners, and each job contains steps that call actions or run shell commands. Typical pipelines include unit tests, linting, build artifacts, and deployment steps targeting staging and production environments.
Step-by-step setup
1. Create the workflow file
Place a YAML file under .github/workflows/ci-cd.yml. Set triggers such as push, pull_request, or workflow_dispatch. Example triggers: branches for feature, develop, main, or tags for releases.
2. Define jobs and use a matrix
Define separate jobs for build, test, and deploy. Use a matrix build to test across Node versions or OS combinations. Matrix jobs speed up coverage and reduce YAML duplication.
3. Cache dependencies and publish artifacts
Use caching (actions/cache) to speed installs and actions/upload-artifact to store build outputs or test reports for later jobs or debugging.
4. Secure secrets and environments
Store credentials and API keys in GitHub Secrets and use Environments for protected deploy targets. Require approvals for production environments when needed.
5. Add deployment job(s)
Add a deploy job that runs after successful tests. Use environment protection rules, or require a manual approval step. For cloud providers, use provider-specific actions or CLI commands.
BUILD-TEST-DEPLOY checklist (named framework)
Use this checklist as a framework to validate a basic pipeline before relying on it:
- BUILD: Install dependencies, run build, cache heavy package installs
- TEST: Run unit tests, integration tests, and collect coverage
- ANALYZE: Lint code, run static analysis, fail on critical issues
- ARTIFACT: Upload build artifacts and test reports
- DEPLOY: Promote artifacts to staging, run smoke tests, then deploy to production
Real-world example: Node.js app with Docker and AWS deployment
Scenario: A Node.js API repository needs CI for tests and a CD pipeline that builds a Docker image and pushes to Amazon ECR, followed by a deployment to ECS or a Kubernetes cluster.
High-level steps in YAML: install Node, run npm test, build Docker image, tag and push to ECR using AWS credentials from GitHub Secrets, then trigger a deployment job that updates the service or applies a new image to the cluster. For provider specifics, refer to the official GitHub Actions docs for Amazon integration: GitHub Actions documentation.
CI CD YAML workflow example
Key parts to include in a CI CD YAML workflow example: name, on (triggers), jobs: build, test, and deploy. Use needs to control execution order and concurrency to avoid double deployments.
Practical tips
- Use matrix builds to test multiple runtime versions without duplicating steps.
- Cache node_modules or package manager stores to reduce build times using actions/cache.
- Upload test results and coverage as artifacts for later inspection with actions/upload-artifact.
- Use environment protection rules and require reviewers for production deployments to limit accidental releases.
- Limit secrets exposure by scoping tokens to minimum required permissions and using token rotation.
Trade-offs and common mistakes
Trade-offs
GitHub-hosted runners require no maintenance but have usage limits and potential cold-start overhead. Self-hosted runners give full control and potentially faster builds for specialized hardware, but require maintenance, security updates, and networking setup. Matrix builds increase test coverage but consume more CI minutes or runner capacity.
Common mistakes
- Committing secrets into the repository instead of using GitHub Secrets.
- Running deploy steps in pull-request workflows—deploy only on protected branches or tags.
- Not failing the pipeline on test failures due to missing exit codes or ignored step results.
- Ignoring artifact retention — set retention periods deliberately to control storage costs.
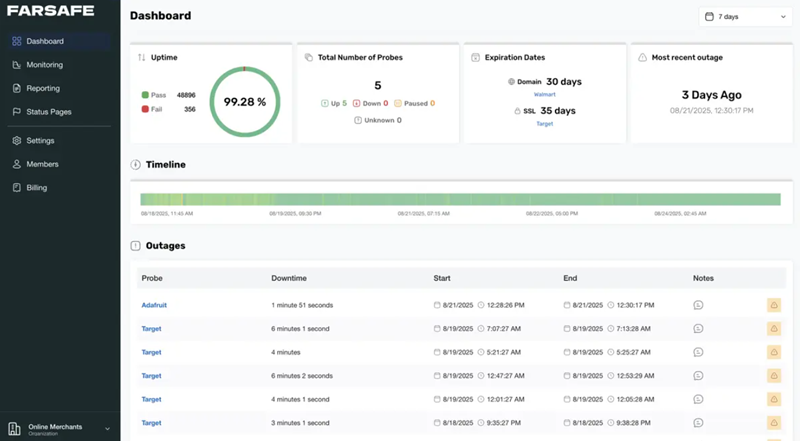
Monitoring, policies, and scaling
Enable workflow run retention and set required checks in branch protection rules. Monitor workflow duration and failure rates to identify flaky tests. Use concurrency and cancel-in-progress to avoid duplicated runs for frequent pushes.
Next steps and extensions
After a working GitHub Actions CI/CD setup, extend pipelines with canary releases, blue/green deployments, or rollout gates integrated with feature flags. Integrate with observability tools to automate rollback on errors.
FAQ: What is the fastest way to get a basic GitHub Actions CI/CD setup running?
Start with a minimal workflow that runs tests on push to main, ensures build success, and uploads artifacts. Add deployment steps later once tests and artifact generation are stable.
FAQ: How to create a GitHub Actions workflow for CI?
Create a YAML file under .github/workflows, define triggers (push, pull_request), add a job with runs-on, steps to checkout code, set up language runtime, install dependencies, run tests, and publish results. Use actions/checkout and actions/setup-node as common building blocks.
FAQ: Can this pipeline deploy to production automatically or require approvals?
Use GitHub Environments to require approvals and limit secrets exposure. For production, enable required reviewers and protection rules to prevent unintended deployments.
FAQ: How to reduce CI run time and cost?
Use dependency caching, selective tests (run fast unit tests on PR, run integration tests on merges), and matrix strategies that balance coverage with runtime. Consider self-hosted runners for heavy builds but account for maintenance overhead.
FAQ: Are there ready-made templates or marketplace actions to speed setup?
Yes, GitHub Marketplace contains community and official actions for many tasks like Docker login, AWS deployments, and test reporters. Use well-maintained actions with clear documentation and review their permissions before adding them to workflows.