Practical Strategies for Overcoming Blockchain App Development Challenges
👉 Best IPTV Services 2026 – 10,000+ Channels, 4K Quality – Start Free Trial Now
Introduction
Building robust blockchain applications requires addressing a distinct set of concerns that differ from traditional software projects. This article describes common obstacles in blockchain app development and presents practical strategies for dealing with scalability, consensus design, smart contract security, interoperability, and regulatory compliance.
- Key technical issues: scalability, latency, smart contract vulnerabilities, and key management.
- Architectural choices: permissioned vs. public ledgers, on-chain vs. off-chain computation.
- Operational practices: testing, monitoring, and upgrade patterns reduce production risks.
- Regulatory and standards guidance: consult public standards bodies and cryptographic best practices.
Common technical challenges in blockchain app development
Scalability and throughput
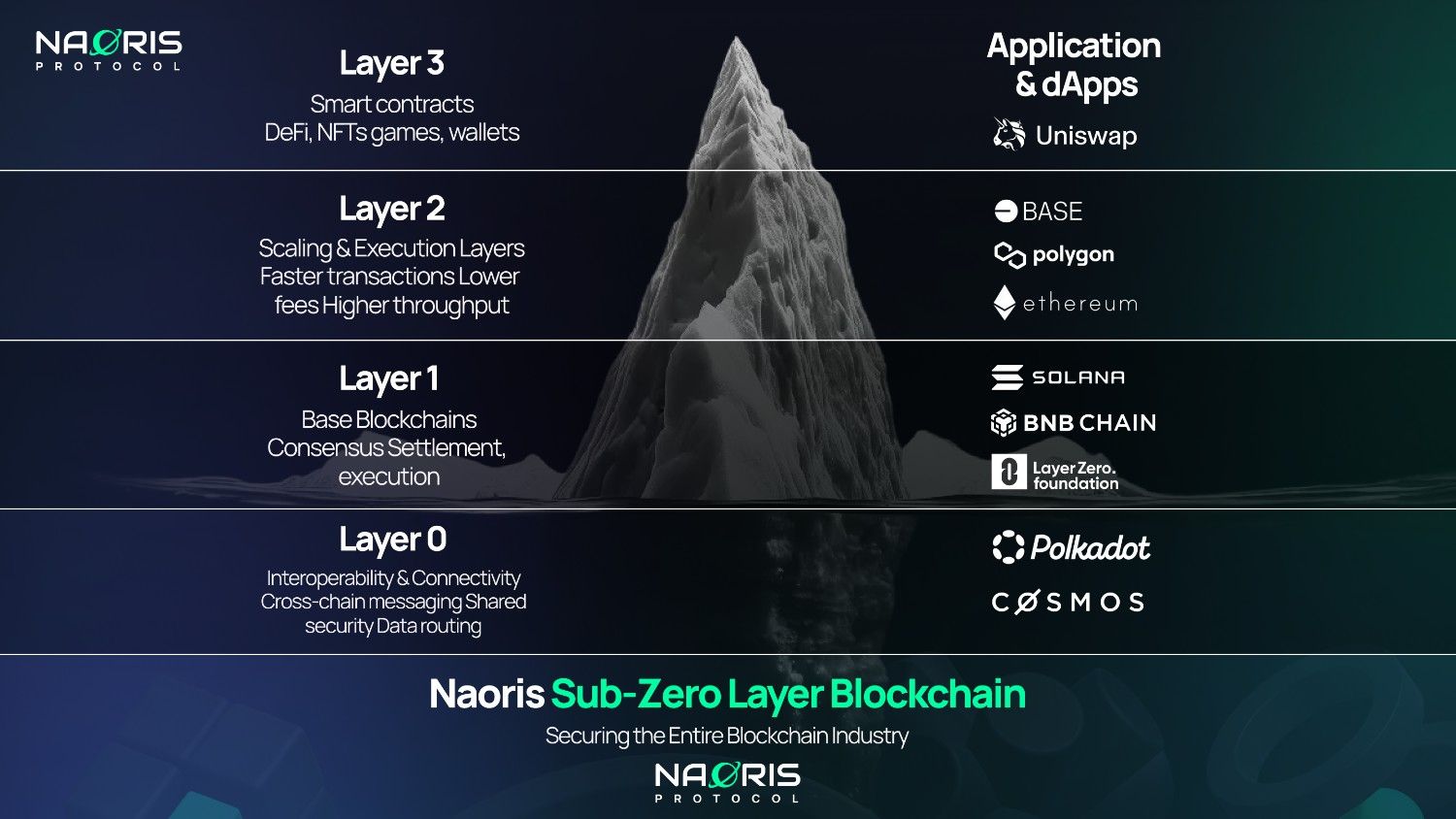
Many blockchain networks trade decentralization or security for throughput. Application requirements for transaction per second (TPS) and confirmation latency should drive selection of consensus mechanisms and layer design. Techniques such as sharding, layer-2 state channels, and batch anchoring can increase effective throughput while keeping on-chain settlement minimal.
Consensus and finality
Consensus mechanisms vary in finality properties and fault tolerance. Understanding whether a use case requires deterministic finality or probabilistic settlement affects architecture choices. For example, permissioned ledgers often provide faster deterministic finality, while some public networks use probabilistic finality that affects user experience and reconciliation.
Smart contract security
Smart contracts are immutable or costly to change in many deployments, creating high risk for coding errors. Static analysis, formal verification where feasible, modular contract design, and multi-signature upgrade patterns reduce risk. Regular security audits and a vulnerability disclosure process are critical.
Key management and privacy
Cryptographic key lifecycle management (generation, storage, rotation, and revocation) is fundamental. Hardware security modules (HSMs), secure enclaves, or enterprise key management services help protect private keys. Privacy concerns may necessitate selective disclosure techniques such as zero-knowledge proofs, confidential transactions, or off-chain data storage with on-chain proofs.
Interoperability and integration
Interfacing with external systems requires reliable oracle designs and standardized data schemas. Cross-chain communication and interoperability protocols help move assets or messages between networks, but they introduce additional trust and attack surface considerations.
Design and architecture considerations
Choose ledger type based on governance
Design decisions should reflect governance and access control requirements. Permissioned ledgers suit enterprise scenarios with known validators and legal accountability, while public ledgers enable censorship resistance and open participation. Hybrid architectures combine on-chain settlement with off-chain computation for performance and privacy.
On-chain vs. off-chain trade-offs
Off-loading heavy computation to off-chain services reduces cost and latency but requires strong integrity guarantees for results. Commit-and-prove schemes, cryptographic receipts, and verifiable computation frameworks help maintain trust without keeping all logic on-chain.
Data modeling and storage
Design the smart contract data model to minimize storage and gas costs. Use references to external storage (content-addressed systems or secure databases) for large files, and store integrity proofs or hashes on-chain to maintain verifiability.
Testing, deployment, and operations
Comprehensive testing strategies
Unit and integration tests for smart contracts must be complemented by simulation of consensus-layer conditions, fork scenarios, and failure injection testing. Continuous integration pipelines that include static analysis and test coverage metrics reduce regression risk.
Deployment and upgrade patterns
Upgradeability patterns—proxy contracts, governance-controlled upgrades, and migration tooling—must balance flexibility with the risk of centralized control. Deployment scripts should be idempotent and auditable. Simulation of migrations in staging environments prevents unexpected state transitions.
Monitoring, incident response, and observability
Observability across the application stack helps detect anomalies quickly. Monitoring should cover node health, mempool behavior, transaction latency, and contract invariants. A documented incident response plan with rollback and mitigation procedures is essential.
Regulatory, governance, and standards
Compliance and data protection
Legal and regulatory requirements vary by jurisdiction and use case. Data protection obligations can influence whether personal data is stored on-chain. Engage legal and compliance specialists early and map data flows to applicable regulations.
Standards and guidance
Standards bodies and research organizations publish guidance on cryptographic practices, interoperability, and risk management. For example, the National Institute of Standards and Technology (NIST) has published resources on blockchain technology and cybersecurity best practices for distributed ledgers; consult that guidance when establishing cryptographic and operational baselines. NIST blockchain technology overview
Strategies and best practices
Start with threat modeling and requirements
Perform threat modeling that covers both consensus-layer and application-layer risks. Define clear success metrics for availability, throughput, latency, and privacy early in the project.
Adopt modular, testable components
Modular design enables independent testing and replacement of components such as consensus plugins, oracle adapters, and storage modules. Use well-reviewed libraries and follow cryptographic best practices from recognized standards organizations and academic literature.
Plan for governance and upgradeability
Establish governance frameworks with defined roles, change control procedures, and emergency response mechanisms. Transparent governance documentation reduces stakeholder uncertainty and supports long-term maintenance.
Invest in developer tooling and education
Developer productivity improves security and reliability. Provide standardized SDKs, linters, testing harnesses, and runbooks. Encourage continuous learning through code reviews, threat workshops, and participation in standards efforts.
Conclusion
Overcoming challenges in blockchain app development requires combined attention to technical, architectural, operational, and regulatory dimensions. Applying principled design, robust testing, and established standards reduces risk and improves the chances of long-term success.
What is blockchain app development and what challenges does it present?
Blockchain app development is the process of designing, building, testing, and operating applications that rely on distributed ledger technology. Challenges include scalability, consensus properties, smart contract security, key management, interoperability, and compliance with regulations and standards.
How can smart contract vulnerabilities be reduced?
Reduce vulnerabilities through code reviews, static analysis tools, formal verification where appropriate, modular contract design, security audits by experienced reviewers, and runtime monitoring of contract invariants.
What architectural choices influence performance and privacy?
Choices include permissioned versus public ledgers, on-chain versus off-chain computation, use of privacy-preserving primitives (e.g., zero-knowledge proofs), and integration of layer-2 scaling solutions. Each choice has trade-offs between throughput, cost, and confidentiality.
How should teams approach regulatory compliance and standards?
Engage legal and compliance expertise early, map data flows for privacy considerations, and align cryptographic and operational practices with guidance from standards bodies and regulators. Refer to public guidance from organizations such as NIST and international standards committees when defining controls.
Are there recommended resources for further learning?
Consult white papers and standards published by recognized organizations in cryptography and distributed systems, academic research on consensus and verifiable computation, and technical guidance from national standards agencies.