Multi-Tenant Architecture: Practical Guide for Scalable SaaS Infrastructure

FREE SEO Topical Map Generator: Find Your Next Content Ideas
Introduction
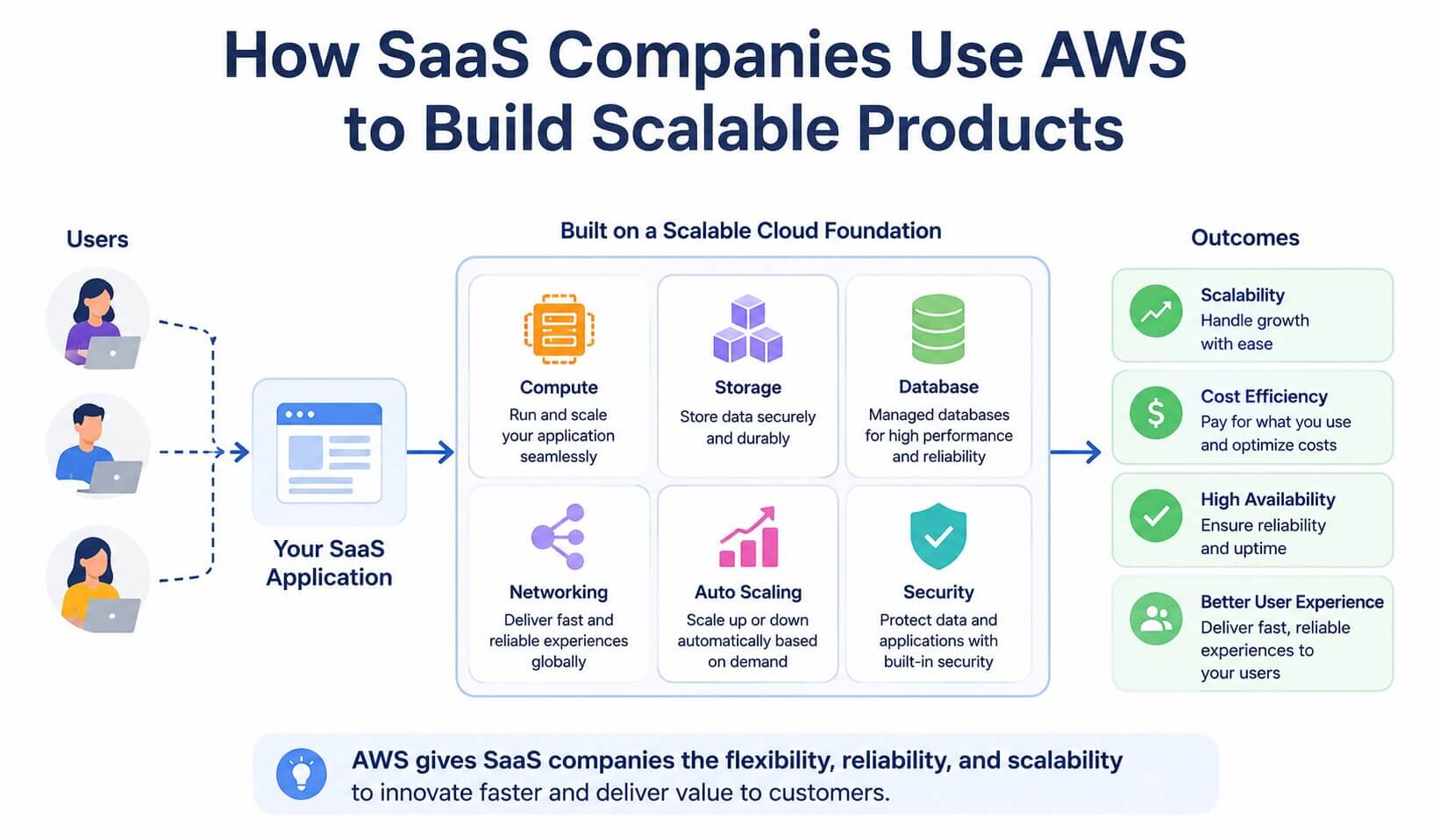
Multi-tenant architecture is a software design approach where a single instance of an application serves multiple customer groups (tenants) while keeping each tenant's data and configuration logically separate. This model is the core of modern SaaS infrastructure because it reduces operational cost per customer, simplifies updates, and supports elastic scaling.
- Multi-tenant architecture shares application resources across customers while enforcing isolation.
- Common patterns: shared schema, schema-per-tenant, database-per-tenant; each has trade-offs for cost, performance, and isolation.
- Use a checklist for security, identity, and resource partitioning; plan for scaling and tenant onboarding.
Multi-tenant architecture: core design patterns
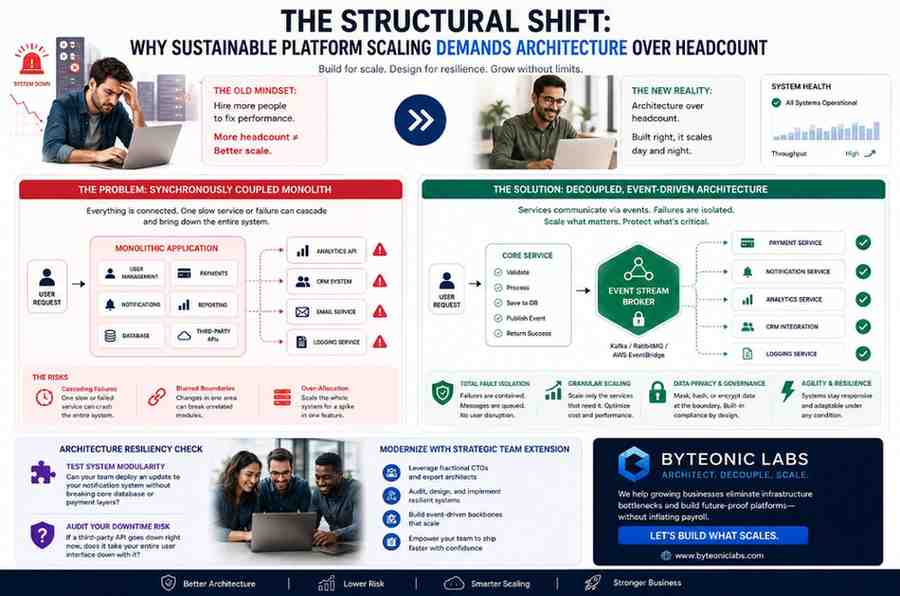
Design choices fall into three primary patterns. Selecting between them affects operational complexity, cost, and security.
SaaS multi-tenancy patterns
- Shared schema (single database, shared tables): All tenants share the same tables; rows contain a tenant_id. Lowest cost and easiest to scale horizontally, but requires careful query and index design to avoid noisy-neighbor effects.
- Schema-per-tenant: One database schema per tenant inside the same DB instance. Better logical isolation and easier per-tenant customization, but schema migrations and management are more complex.
- Database-per-tenant: Each tenant gets its own database instance. Best isolation and compliance; highest operational and resource cost, often used for large or regulated customers.
Tenant isolation strategies
Isolation occurs at multiple layers: data, network, compute, and control plane. Common tenant isolation strategies include row-level security and tenant-aware queries for shared schemas, separate schemas or databases for stronger isolation, and network segmentation or dedicated VPCs for top-tier customers.
TIERS checklist: a practical framework for designing multitenancy
Use the TIERS checklist to evaluate architecture decisions and implementation steps:
- Tenant Identification: enforce a consistent tenant_id in auth tokens and requests.
- Identity & Access: integrate tenant-aware RBAC and centralized identity (SSO, OAuth).
- Encryption & Data Protection: encrypt data at rest and in transit, use per-tenant keys where required.
- Resource Partitioning: define compute and storage limits, rate limits, and quotas per tenant.
- Scaling & Observability: plan autoscaling, tenant-level metrics, and alerting for noisy neighbors.
Real-world example: analytics SaaS serving SMBs and enterprises
A SaaS analytics provider starts with a shared schema to minimize cost for hundreds of small businesses. As enterprise customers join, the product offers schema-per-tenant and database-per-tenant tiers for strict compliance and performance isolation. Operationally, migrations use feature flags and blue-green deploys; monitoring tags tenant queries so a noisy tenant can be throttled without affecting others.
Practical tips for building secure, scalable multi-tenant systems
- Instrument tenant-aware observability: collect per-tenant latency, error rate, and resource usage to detect noisy neighbors early.
- Adopt tenant-aware access tokens: include tenant_id in signed tokens and validate at each service boundary.
- Automate lifecycle operations: provisioning, backups, migrations, and onboarding should be automated to avoid human error.
- Plan database sharding by tenant size, not just count: group tenants by expected usage to balance load.
Trade-offs and common mistakes
Major trade-offs
- Cost vs. isolation: shared-schema is cheap but weaker isolation; database-per-tenant is costly but strong isolation and compliance support.
- Operational complexity vs. customization: schema-per-tenant allows customization but increases migration complexity.
- Performance vs. manageability: high isolation prevents noisy neighbors but increases backup, scaling, and maintenance overhead.
Common mistakes to avoid
- Missing tenant scoping in queries — forgetting WHERE tenant_id = ? can expose data across tenants.
- Underestimating noisy neighbors — lack of per-tenant quotas leads to one tenant affecting all.
- Lack of automation for schema changes — manual migrations across many schemas or DBs cause downtime and errors.
Standards and compliance considerations
Design choices should align with standards for cloud security and data protection. For definitions and baseline cloud concepts, refer to official guidance such as the NIST cloud definition. For regulatory compliance, map tenant isolation and encryption practices to applicable laws (e.g., GDPR, HIPAA) and to internal audit controls.
When to choose multi-tenancy
Multi-tenant architecture fits products aiming for high customer density and frequent updates. Choose single-tenant or hybrid approaches when customers require strict isolation, dedicated resources, or unique customizations that are impractical at scale.
FAQ
What is multi-tenant architecture and why use it?
Multi-tenant architecture lets one application instance serve multiple customers with logical separation. It reduces per-customer cost, centralizes updates, and simplifies operations, making it suitable for many SaaS businesses.
How do SaaS multi-tenancy patterns affect database design?
Shared schema favors lower cost and simpler scaling, schema-per-tenant balances isolation with manageability, and database-per-tenant offers the strongest isolation at higher operational cost. Choose based on tenant size, compliance needs, and operational capacity.
What are effective tenant isolation strategies?
Combine logical controls (tenant_id scoping, RBAC), encryption (per-tenant keys if required), and infrastructure isolation (separate VPCs or databases for high-risk tenants) to manage isolation effectively.
How should multitenant systems handle noisy neighbors?
Implement per-tenant quotas, rate limiting, throttling, and priority scheduling. Monitor tenant-level metrics and use autoscaling and resource capping to protect overall system health.
When is single-tenant preferable to multitenant?
Choose single-tenant for customers with unique compliance requirements, heavy customization, or predictable large resource needs that justify dedicated infrastructure and operational cost.