Open Source License Checker: How to Run License Compliance Checks in Projects

Get a free topical map and start building content authority today.
An open source license checker inspects a project's source code, dependencies, and build artifacts to identify license terms that affect distribution, modification, and commercial use. Use a license checker early and often to avoid unexpected obligations, build an accurate software bill of materials (SBOM), and document decisions for audits or distributors.
Use an open source license checker to automate license identification, apply a repeatable review checklist, and integrate checks into development pipelines. Key outputs: license list, risk flags, remediation plan, and SBOM with SPDX identifiers.
open source license checker: what it does and why it matters
Definition and outputs
A license checker parses dependency manifests (package.json, pyproject.toml, go.mod, etc.), inspects source files and packaged artifacts, and maps findings to standard license identifiers. Typical outputs include a license inventory, matched SPDX identifiers, detected license conflicts (for example, copyleft vs permissive), and a confidence score for each match.
Standards and organizations
Use SPDX identifiers and formats for reporting to improve clarity and interoperability. SPDX is maintained as a community standard; see the SPDX project for format and identifier guidance: https://spdx.org/.
How to run a license checker in a project
Step-by-step implementation
- Inventory: Generate a dependency list and initial SBOM from package metadata and lock files.
- Scan: Run the license checker to detect license text and map to SPDX identifiers.
- Analyze: Compare detected licenses to the project's license policy (allowed, restricted, forbidden).
- Remediate: Replace, isolate, or obtain additional permissions for disallowed dependencies.
- Document: Produce an SPDX-compatible SBOM and log decisions for future audits.
LICENSE SAFE checklist (named framework)
Apply the LICENSE SAFE checklist to standardize reviews:
- Scan — Run automated license scanning across all components and build artifacts.
- Assess — Map licenses to policy categories and flag conflicts or obligations.
- Notify — Alert maintainers and stakeholders with clear remediation tasks.
- Enforce — Block builds or merges that introduce forbidden licenses in CI if policy requires.
- Secure — Archive the SBOM and approval records for audits and redistribution.
- Automate — Integrate checks in pre-merge and release pipelines for ongoing control.
Practical example: web app dependency scan
A web application uses npm and dozens of indirect dependencies. A license checker running in CI identifies an indirect dependency declared under GPL-3.0-only, which the project's policy forbids for distributed artifacts. Using the LICENSE SAFE checklist, the team:
- Scans the full dependency tree and confirms the package introducing the GPL-3.0-only license.
- Assesses alternatives: updates to a permissive fork, replacing the dependency, or obtaining a commercial license if available.
- Remediates by replacing the package with an MIT-licensed alternative and updates the SBOM with SPDX identifiers and the decision note.
Practical tips for effective license compliance scanning
- Run license compliance scanning early (pre-merge) and on every release to avoid late surprises.
- Use SPDX identifiers in reports to make license metadata machine-readable and consistent across tools.
- Combine automated scanning with a manual review for ambiguous or low-confidence matches—automated tools miss context like dual-licensing or patent clauses.
- Integrate the checker with CI to fail builds only for high-risk findings; surface lower-risk findings as warnings to avoid blocking productivity.
Trade-offs and common mistakes
Trade-offs
Automation speed vs. accuracy: Automated license checkers provide coverage fast but can misclassify or miss embedded license text. Manual review adds accuracy but increases cost and time. Policies that are too strict may block useful dependencies; policies that are too permissive increase legal exposure.
Common mistakes
- Assuming package metadata is correct—many packages omit license files or mislabel licenses.
- Ignoring transitive dependencies—indirect packages can introduce restrictive terms.
- Not documenting exemptions and approvals, which makes audits costly and repeat investigations likely.
Integration and automation patterns
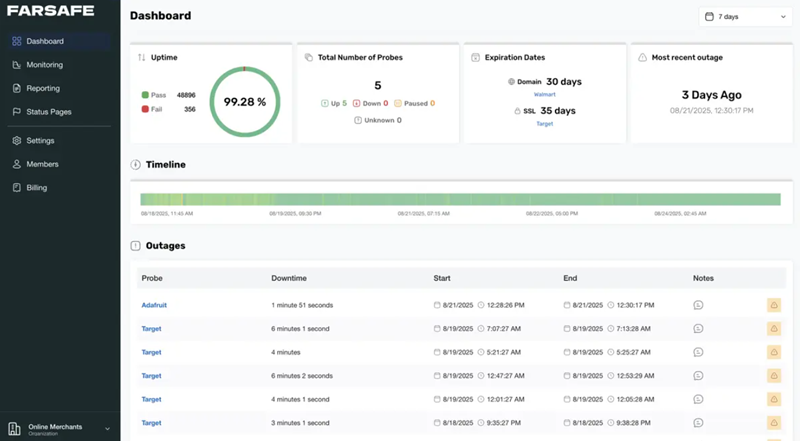
Integrate an open source license checker with CI/CD for continuous enforcement. Common patterns: pre-merge scanning with a results dashboard, gated releases that require a clean SBOM, and nightly full-repo scans to catch changes in transitive dependencies. Record SPDX-based SBOMs alongside release artifacts so downstream consumers can verify license obligations.
When to involve legal or compliance teams
Escalate findings when a discovered license imposes distribution obligations (copyleft), patent provisions, or unclear dual licensing. Legal review is required for contract negotiation, commercial relicensing, or when the team cannot find a safe replacement.
FAQ
What is an open source license checker and how accurate is it?
An open source license checker is an automated tool that detects and reports license declarations and license text in code and dependencies. Accuracy varies by tool and repository: look for tools that match license text to SPDX identifiers and provide confidence scores. Always follow up automated results with a focused manual review for low-confidence findings.
How does a license checker support an SBOM (software bill of materials)?
License checkers produce SPDX-compatible outputs listing packages, versions, and license identifiers. Include those outputs in the SBOM to make license obligations discoverable for downstream consumers and auditors.
Can license scanning replace legal review?
No. License scanning automates discovery and triage but does not replace legal analysis when obligations are ambiguous, when code is dual-licensed, or when commercial licensing discussions are needed.
How to handle a flagged incompatible license in a dependency?
Options include replacing the dependency, isolating the functionality behind a service boundary, requesting a relicense, or obtaining permission from the copyright holder. Document the decision and update the SBOM.
Which SPDX identifiers and formats should a license checker produce?
Produce SPDX license identifiers, file-level license mappings when possible, and an SPDX document for the component or release. SPDX is the recommended standard for consistent license reporting and downstream consumption.
For further reference on identifiers and the SPDX document format, consult the SPDX project documentation: https://spdx.org/.