Practical Tech Stack Guide for Solo SaaS Developers: Choose, Build, and Scale

Get a free topical map and start building content authority today.
Choosing a practical, maintainable tech stack matters more than chasing the latest trend. This guide explains how to evaluate options and assemble a reliable tech stack for solo SaaS developer projects that balance speed, cost, and long-term operability.
- Prioritize developer productivity, predictable costs, and simple operations.
- Use the SaaS Solo Stack Decision Framework (S3DF) to choose core components.
- Start small: API, auth, storage, and billing; make each replaceable later.
- Follow security best practices and automate backups and monitoring.
Choosing the right tech stack for solo SaaS developer
Decision criteria drive good stacks: how fast can a minimum viable product (MVP) be built, how predictable are costs, and how easy is maintenance alone. Key areas to evaluate: frontend, backend, database, auth/billing, deployment, and observability. Each choice affects time-to-market, run costs, and technical debt.
SaaS Solo Stack Decision Framework (S3DF)
The S3DF is a simple checklist to evaluate each component against four dimensions: Speed, Cost, Reliability, and Replaceability (SCRR). Score each candidate 1–5 on SCRR and prefer components with consistently high marks across dimensions.
S3DF checklist
- Speed — How quickly can the developer build features?
- Cost — What are predictable monthly and scaling costs?
- Reliability — Is the service mature and well-documented?
- Replaceability — How easy is it to swap the piece later?
Core components and trade-offs
Frontend
Choices: server-rendered pages, SPA with a JavaScript framework, or static sites with dynamic APIs. Trade-off: faster UX and richer interactions cost more front-end complexity. For many solo builders, a server-rendered or hybrid approach reduces build and maintenance time.
Backend and APIs
Options include frameworks (lightweight or full-stack), managed backends, or low-code backend platforms. Evaluate the low-code backend for SaaS options when speed matters, but beware of lock-in if product requirements become complex.
Databases and persistence
Postgres-compatible relational databases are a common default for SaaS due to ACID guarantees and flexible schemas. NoSQL can simplify certain scaling patterns but often increases upfront complexity.
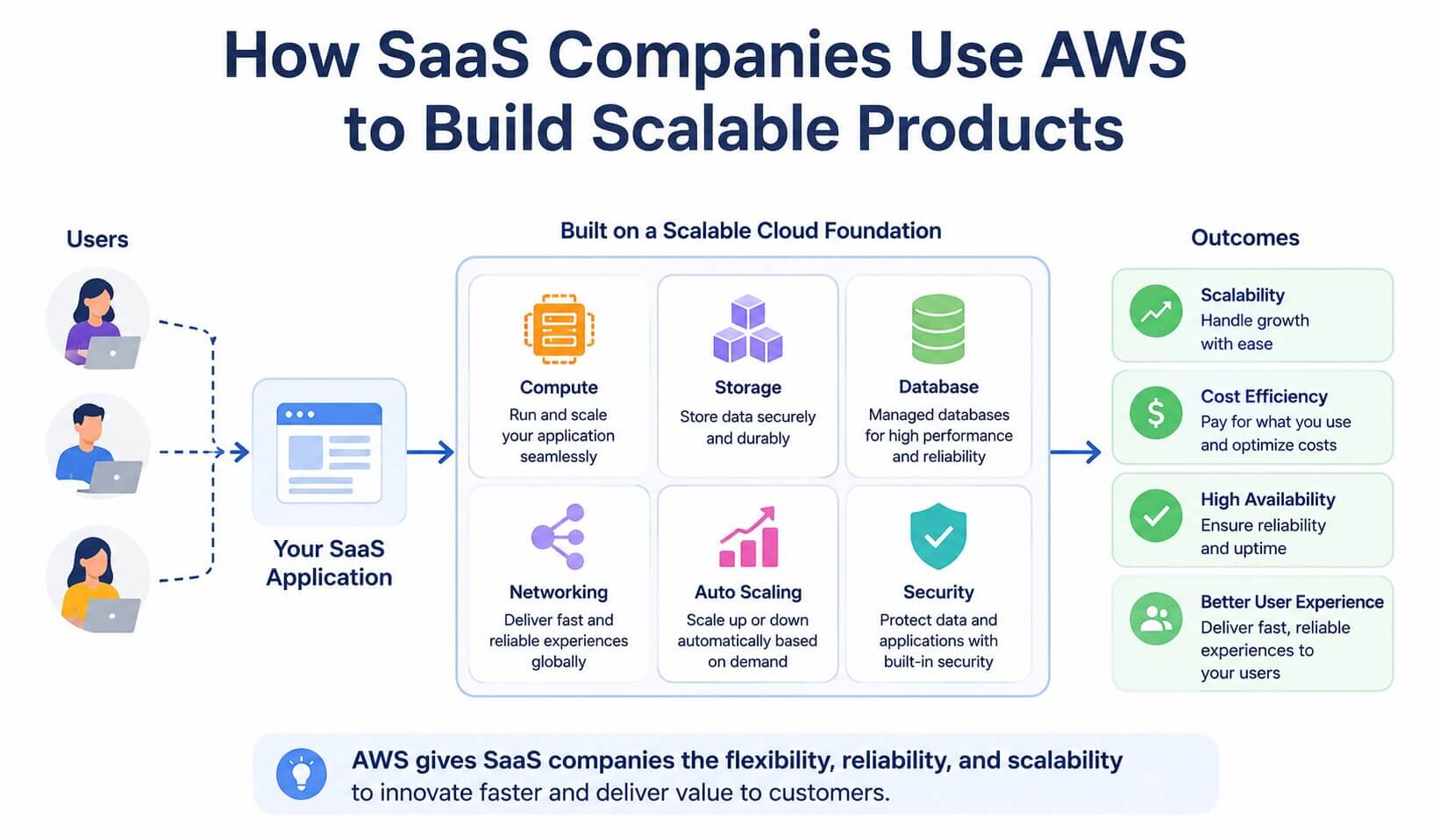
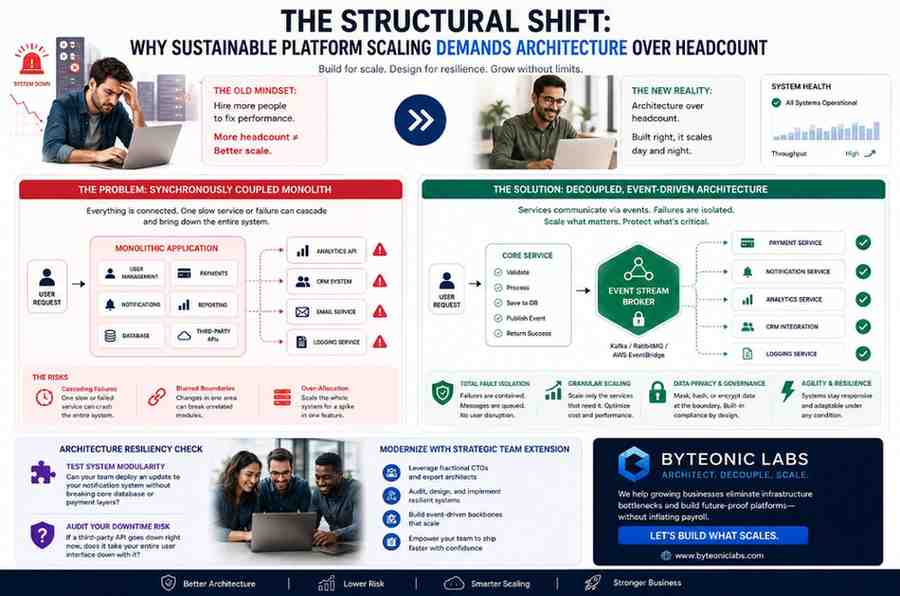
Hosting: serverless vs containers
Serverless reduces operational overhead and can be cost-efficient at low traffic, while containers make resource usage more predictable at scale. This is the classic serverless vs containers for startups decision: serverless for rapid MVPs, containers for steady predictable growth.
Auth, billing, and third-party services
Use battle-tested auth solutions and payment providers to avoid reinventing flows and compliance. Outsourcing these reduces development time but adds recurring costs and increases external dependency surface.
Observability and security
Automated logging, error tracking, and uptime alerts are essential. Adopt baseline security controls early: least-privilege on services, TLS everywhere, and automated backups. Follow community-endorsed practices such as those published by OWASP for secure defaults.
Real-world example scenario
Example: a solo developer launching a subscription-based analytics tool. Using the S3DF, the developer chooses a server-rendered frontend to minimize complexity, an API built with a lightweight web framework, Postgres for storage, a managed auth service for sign-ins, and serverless functions for background processing. Costs are low at launch, and components are selected for replaceability to allow migration to containerized services as user load grows.
Practical tips
- Automate deployments and database backups before user sign-ups—manual ops become bottlenecks.
- Keep interfaces well-defined (API contracts) so replacing a service later is manageable.
- Instrument metrics from day one: simple request latency, error rate, and cost-per-customer reveal issues early.
- Limit custom infrastructure: prefer managed services until scale forces alternatives.
- Use feature flags to roll out changes safely and decouple deployments from releases.
Common mistakes and trade-offs
Common mistakes
- Overengineering: building complex infrastructure instead of shipping features.
- Underinvesting in backups and recovery—data loss is irreversible for customers.
- Locking into proprietary low-code platforms without migration plans.
Trade-offs to accept early
- Accept slightly higher per-user costs from managed services to reduce operational load.
- Choose predictable performance over micro-optimizations that complicate the stack.
- Defer deep optimization until clear bottlenecks appear in production metrics.
Checklist before launch
- Automated CI/CD and rollback plan
- Daily backups and tested restore procedure
- Basic monitoring and alerting for errors and latency
- Secure defaults for auth, data storage, and transport
- Cost estimates for expected usage tiers
FAQ
What is the best tech stack for solo SaaS developer to start with?
There is no single best stack. Prioritize stacks that maximize developer productivity and replaceability: a minimal web frontend, a simple REST or GraphQL API, a relational database like Postgres, managed auth and payments, and a deployment strategy that automates builds and rollbacks.
How do serverless and containers compare for an MVP?
Serverless lowers operational burden and suits bursty workloads and low baseline traffic; containers give predictable performance and cost at steady loads. Choose serverless to move fastest, switch to containers when costs or performance require it.
When should a solo developer migrate away from managed services?
Migrate when costs, performance, or feature needs consistently exceed what managed services can provide and when the time investment to manage self-hosted alternatives is justified by business value.
How to estimate costs for a cost-effective SaaS architecture?
Estimate per-customer usage (API calls, storage, bandwidth) and map that to provider pricing. Include overhead for logs, backups, and monitoring. Revisit estimates monthly and build budget alerts into billing.
What security basics must a solo SaaS developer implement?
Enforce TLS, secure authentication, least privilege for service accounts, input validation, and automated backups. Follow established guidance such as OWASP recommendations for web application security.