Practical Guide: Automating Pull Request Feedback with an AI Code Reviewer

FREE SEO Topical Map Generator: Find Your Next Content Ideas
An AI code reviewer for pull requests can automate routine feedback, surface security and style issues early, and let engineers focus on design and architecture. This guide explains what an AI reviewer does, how to implement one in an automated code review workflow, and how to avoid common pitfalls.
- Define goals for automated feedback: correctness, style, security, tests.
- Follow the R.E.V.I.E.W. checklist to stage and approve AI suggestions.
- Integrate the reviewer into CI/CD and choose guardrails for false positives.
- Measure impact using merge time, comment relevance, and revert rate.
How to implement an AI code reviewer for pull requests
Start by mapping existing review tasks that are repetitive or rules-based. An AI code reviewer for pull requests can generate inline comments, suggest refactors, and flag potential security issues. Prioritize tasks that save reviewer time without risking incorrect changes, such as linting fixes, naming suggestions, and detecting missing tests.
Define scope and acceptance criteria
Clear scope prevents noisy automation. Decide which comment types are allowed (e.g., style vs. logic), how suggestions are presented (automated fix vs. comment), and who approves automated changes. Use measurable acceptance criteria: comment precision > 70%, false positive rate < 10%, and reviewer adoption rate.
R.E.V.I.E.W. checklist (named framework)
Use the R.E.V.I.E.W. checklist to evaluate AI suggestions before they are applied or surfaced to engineers.
- Relevance: Is the suggestion relevant to the PR goal?
- Evidence: Does the suggestion include reasoning or a pointer to docs or tests?
- Verifiability: Can the suggestion be validated by tests or CI jobs?
- Impact: What is the risk of applying the change automatically?
- Explainability: Is the suggestion understandable to the reviewer?
- Warning threshold: Should the suggestion be a warning, blocking comment, or auto-applied fix?
Implementation steps (procedural)
1. Choose integration points
Decide whether the AI reviewer runs as a pre-commit hook, a CI job, or a repository bot that comments on pull requests. Each option affects latency and developer experience. For example, running in CI provides context and tests; running as a pre-commit hook reduces bad commits earlier.
2. Combine tools: static analysis + AI
Combine deterministic tools (linters, static analyzers, security scanners) with the AI reviewer. Let deterministic checks block merges, and let AI provide suggestions where rules are fuzzy. This hybrid model reduces false positives and leverages the strengths of each approach.
3. Gate suggestions
Start with non-blocking comments, then move to auto-fixes for low-risk items. Require human approval for suggested logic changes. Maintain audit logs for automated changes.
4. Integrate into CI/CD
Hook the reviewer into CI/CD pipelines (e.g., run as part of the pull-request job). Example CI patterns include running an AI-checker job after tests pass to avoid wasted compute on failing builds.
Reference implementation details and pull request workflows in official docs: GitHub Pull Requests documentation.
Short real-world example
Scenario: A backend team adds an AI reviewer that detects missing input validation. The pipeline runs unit tests, then the AI reviewer examines changed files and posts comments that include a short code sample and a reference to the validation guideline. Developers accept the suggestion, add a small validation helper, and the subsequent CI job passes. After three months the team tracks a 20% drop in related bug reports and reduced reviewer load on repetitive checks.
Practical tips
- Start with one repository and one class of suggestions (style or docs) before expanding.
- Store configuration as code (YAML) so teams can tune thresholds per repo or team.
- Keep suggestions concise: one actionable change per comment with a clear reason.
- Monitor and log AI decisions to allow rollback and auditing of automated fixes.
Trade-offs and common mistakes
Trade-offs
- Noise vs. coverage: aggressive suggestions increase coverage but raise noise and distrust.
- Latency vs. context: running in pre-commit lowers feedback loop but misses CI test context.
- Automation vs. oversight: automatic fixes save time but can introduce subtle bugs if not verified.
Common mistakes
- Applying large refactors automatically without tests or code owner approval.
- Failing to tune suggestions to project style leading to low adoption.
- Relying solely on AI for security checks instead of combining with dedicated scanners.
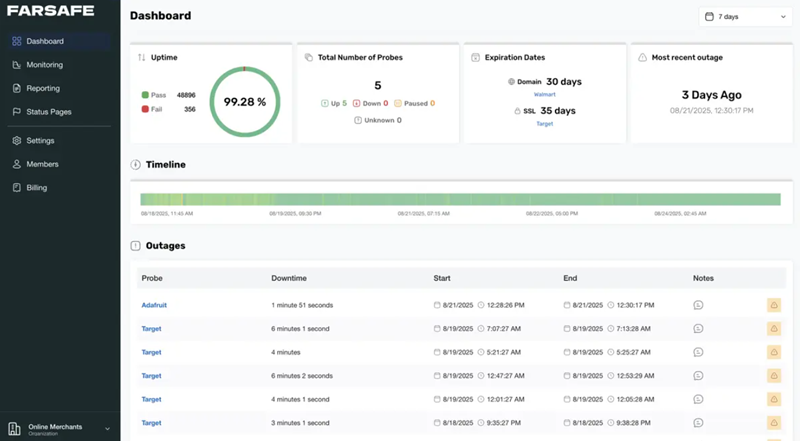
Metrics to measure success
Track these indicators: time-to-merge, number of reviewer comments per PR, percentage of AI suggestions accepted, revert rate for automated changes, and security findings caught pre-merge. Regularly review these metrics to adjust thresholds and scope.
Frequently asked questions
What is an AI code reviewer for pull requests and when should teams use one?
An AI code reviewer for pull requests is a system that analyzes code changes and produces inline feedback or automated fixes. Use it for repetitive checks (style, small refactors, doc updates), to surface potential security or test gaps, and to scale review capacity without replacing human judgment.
How to reduce false positives from AI suggestions?
Combine deterministic checks, restrict suggestions to low-risk changes initially, require explainability in comments, and tune the model using a labeled dataset of accepted vs. rejected suggestions from the team.
Can automated fixes be applied safely?
Auto-apply only low-risk changes (formatting, imports, lint fixes) and require tests or human approval for logic changes. Keep a rollback mechanism and audit trail for all automated commits.
What are best practices for CI/CD code review integration?
Run the AI reviewer after tests to avoid wasting compute, expose configuration per-repo, and surface suggestions as non-blocking comments until confidence is established. Use metrics to promote suggestions to blocking checks when safe.
How to combine AI feedback with existing static analysis and security scanners?
Use static analyzers as the primary gate for deterministic issues, let the AI suggest improvements that static tools miss, and ensure security scanners run separately for in-depth checks. This layered approach reduces overlap and improves signal quality.