Practical Guide to Development Environment Setup: Local, Staging & Production

FREE SEO Topical Map Generator: Find Your Next Content Ideas
A clear development environment setup saves time, reduces outages, and makes deployments predictable. This guide explains the common roles for local, staging, and production environments, how they differ, and an actionable checklist teams can use to standardize releases. The primary goal: make changes safe to test locally, reliable to validate in staging, and repeatable when deployed to production.
Development environment setup: roles and definitions
Development environment setup typically divides into three tiers: a local environment for developers, a staging environment for validation, and a production environment for live users. Each tier has different requirements for performance, security, data fidelity, and access control. Clarifying those roles prevents accidental data leaks, configuration drift, and unexpected behavior at release time.
Local development environment
Purpose and expectations
The local development environment is for fast feedback: code editing, unit tests, and early debugging. It should be easy to reproduce on any developer machine, start quickly, and avoid depending on production services that are costly or rate-limited.
Typical setup
Common elements include a local database instance or a lightweight in-memory substitute, dependency management (package.json, Pipfile, etc.), and reproducible environments using containers or versioned VM images. Using feature branches and isolated database fixtures helps keep local work independent.
Staging vs production environment
Staging environment purpose
Staging mirrors production properties: configuration, external integrations, and data shape—without live traffic. Staging is the final verification point for integration tests, performance checks, and regulatory reviews.
Production environment characteristics
Production serves real users. Requirements include monitoring, error reporting, backups, security hardening, and a reliable rollback plan. Performance and availability SLAs are enforced here.
Named framework: LSPP checklist
Introduce the LSPP checklist (Local → Staging → Preflight → Production) as a repeatable framework to standardize releases. Use this checklist before merging and deploying:
- Local: Static analysis and unit tests pass; environment-specific configs use placeholders.
- Staging: Integration and end-to-end tests pass; performance smoke tests run on production-like data.
- Preflight: CI build artifacts verified, migration scripts validated, and rollback plan documented.
- Production: Monitor health checks, apply migration during low traffic, and verify post-deploy metrics.
Practical example: small web app release scenario
A three-person team develops a customer portal. Developers use containers and seeded test data locally for feature work. A continuous integration pipeline runs unit tests and builds artifacts. When a feature branch is ready, it is deployed to a staging environment that uses anonymized production-like data. QA runs integration and exploratory tests in staging. After staging sign-off, an automated preflight job runs database migration dry-runs and smoke tests; then the artifact is deployed to production during a scheduled window with monitoring and rollback scripts ready.
Practical tips (actionable)
- Automate environment provisioning using infrastructure-as-code so staging mirrors production reliably.
- Keep secrets out of source control: use a secrets manager and inject at runtime per environment.
- Run automated tests in CI for every push; require green builds before merging to the main branch.
- Maintain a stable migration path: always include idempotent database migrations and a tested rollback plan.
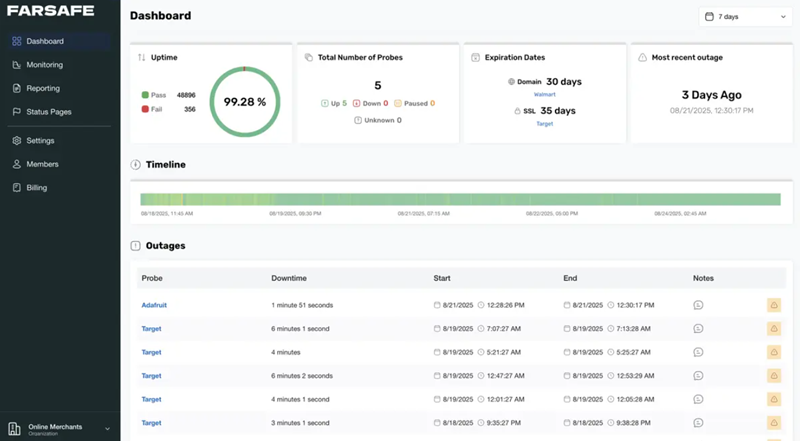
- Use health checks and synthetic monitoring immediately after deployment to validate user-facing behavior.
Common mistakes and trade-offs
Common mistakes
- Testing only on local machines: leads to configuration drift and “works on my machine” failures.
- Using production data directly in staging without anonymization, which risks privacy and compliance violations.
- Manual deployment steps: increases human error and slows recovery from incidents.
Trade-offs
Maintaining multiple environments increases operational overhead. A highly faithful staging environment is more expensive but reduces surprises. For small teams, a combined staging+preflight environment can be a cost-savvy compromise if paired with strong automated tests and feature flags.
Security and standards
Production must follow established security practices: least privilege for credentials, encrypted transport, and routine vulnerability scans. For secure configuration guidance and common vulnerability frameworks, refer to OWASP for baseline checks and recommendations: https://owasp.org.
Checklist before every production release
- CI build artifact verified and immutable.
- Automated tests (unit, integration, e2e) passed in staging.
- Database migrations dry-run and backup completed.
- Monitoring alerts and dashboards ready; runbooks accessible.
- Rollback plan tested and documented.
FAQ: What is the best development environment setup for a web app?
The best development environment setup balances speed and fidelity: use reproducible local environments for fast iteration, a staging environment that mirrors production for validation, and automated preflight checks to catch regressions before production. Apply the LSPP checklist to reduce risks.
How should a local development environment differ from staging?
Local environments prioritize speed and developer productivity; they often use lighter-weight services and mocked integrations. Staging should replicate production behavior—real services, similar data shapes, and configuration parity—so it validates the full stack prior to release.
When is it okay to combine staging and pre-production?
Combining is acceptable for small teams when running thorough automated tests and using feature flags. The trade-off is less isolation; stronger testing and runbooks mitigate the added risk.
How to manage secrets across environments?
Use a centralized secrets manager with environment-specific access policies. Avoid storing secrets in source code or container images; inject them at runtime via secure pipelines or orchestration platforms.
How can deployment failures be minimized?
Minimize failures by automating builds and tests, running migrations in safe modes, deploying during low-traffic windows, and having a rehearsed rollback plan. Use feature flags to decouple deployment from release when possible.